Blog
Featured Topics
-

Detecting Insider Threats
Insider threats represent the most challenging adversary class for any security architecture. Unlike external attackers who must first gain access,…
-
SIEM Integration for Zero Trust
A Security Information and Event Management (SIEM) platform is the analytical backbone of any Zero Trust deployment. While Zero Trust…
-
Logging and Auditing in Zero Trust
In a perimeter-based security model, logging was often an afterthought: a compliance checkbox that generated gigabytes of data rarely reviewed…
-
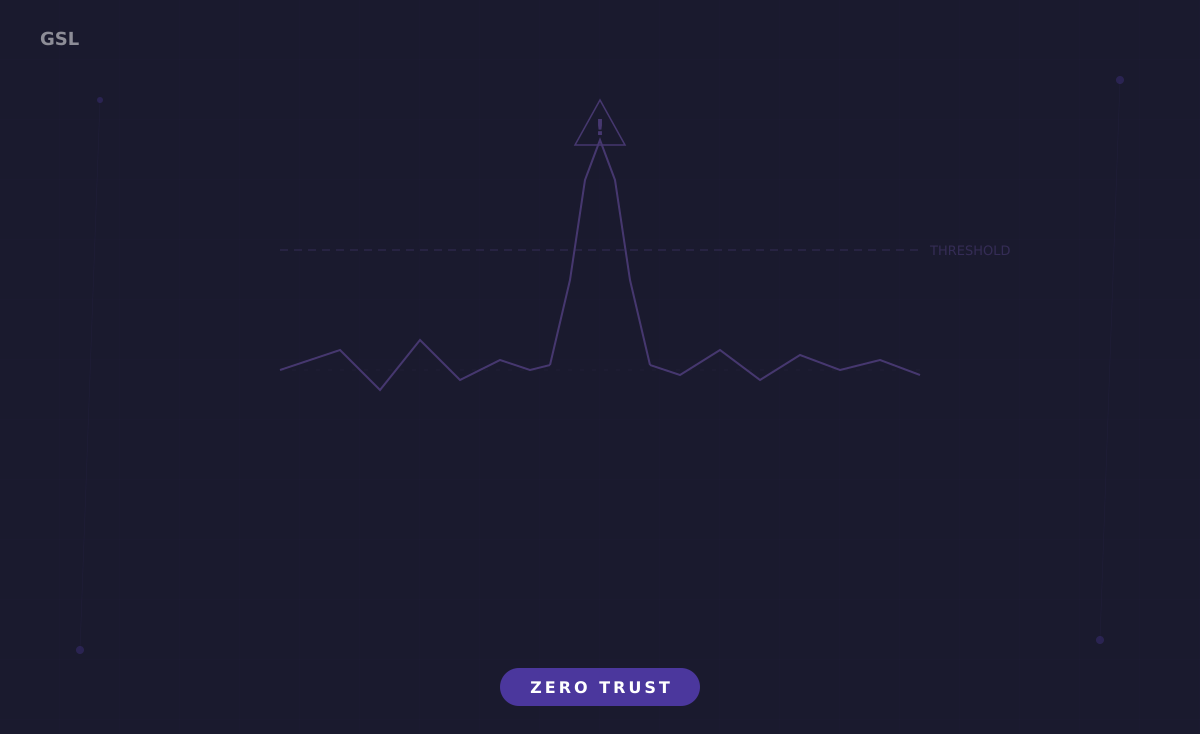
Behavior-Based Anomaly Detection
For decades, security teams relied on signature-based detection: known-bad indicators matched against traffic and log data. This approach fails in…
-
Continuous Authentication Explained
Traditional authentication models operate on a simple binary assumption: once a user proves their identity at the login gate, they…
-
Zero Trust for Mobile Devices
Mobile devices represent the most dynamic and diverse endpoint category in modern enterprise environments. Smartphones and tablets running iOS and…
-

Managing IoT Devices in Zero Trust
Internet of Things devices present a fundamental challenge to Zero Trust architectures. The core Zero Trust principle, verify every device…
-
Endpoint Telemetry and Continuous Verification
Traditional access control evaluates device state once, at authentication time, and then trusts the device for the duration of the…
-
Blocking Non-Compliant Devices Automatically
Manual remediation of non-compliant devices does not scale. In an enterprise with tens of thousands of endpoints, security teams cannot…