Blog
Featured Topics
-
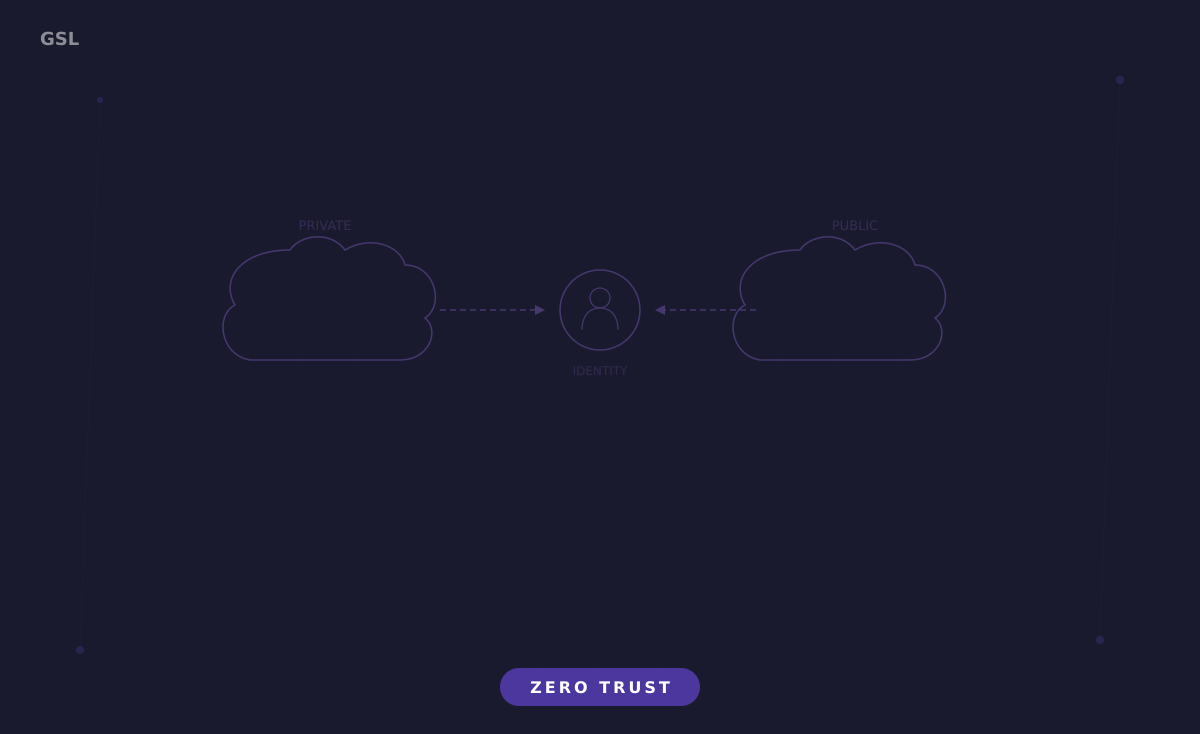
Hybrid Cloud Identity Federation
Hybrid cloud environments introduce a fundamental identity challenge that single-cloud deployments never face: a single user or workload needs authenticated…
-

Zero Trust in GCP
Google Cloud Platform holds a unique position in the Zero Trust landscape because Google invented the modern concept with BeyondCorp,…
-

Zero Trust in Azure
Microsoft Azure has built its cloud platform with Zero Trust as a first-class design principle, largely driven by Microsoft’s own…
-

Zero Trust in AWS
Amazon Web Services operates on a shared responsibility model where AWS secures the infrastructure, but customers own the security of…
-

Validating Zero Trust with Red Team Exercises
A Zero Trust architecture can look flawless on paper: micro-segmentation policies defined, identity verification enforced at every access point, device…
-

Threat Hunting in a Zero Trust Network
Traditional threat hunting assumes a clear boundary between trusted and untrusted space. Hunters focus on finding adversaries who have penetrated…
-

Automating Incident Response
Zero Trust architectures generate security events at a volume and velocity that exceed human processing capacity. When a compromised credential…
-

Security Telemetry Architecture
Security telemetry is the structured collection of observable data from every layer of your infrastructure, identities, endpoints, networks, applications, and…
-
Real-Time Risk Scoring Models
Traditional access control operates on static rules: if a user belongs to group X and the resource is classified as…