What Are Device Posture Checks?
Device posture checks are real-time evaluations of an endpoint’s security state before granting access to corporate resources. Unlike traditional network perimeter defenses that implicitly trusted any device on the corporate LAN, Zero Trust architectures treat every connection request as potentially hostile. The device posture check acts as the first gate in this verification chain, interrogating the endpoint for compliance with organizational security policies before any application-layer communication is permitted.
At its core, a posture check queries the device for a defined set of attributes: operating system version, patch level, disk encryption status, firewall state, presence of an approved EDR agent, and certificate validity. These attributes are collected by a lightweight agent running on the endpoint and transmitted to a policy decision point (PDP) that evaluates them against a policy set. If the device fails any required check, access is denied or downgraded to a restricted resource set.
Architecture of a Posture Assessment Pipeline
A well-designed posture assessment pipeline operates in three distinct phases: collection, evaluation, and enforcement. During the collection phase, the endpoint agent gathers telemetry from the operating system, installed software inventory, running processes, and hardware security modules. This data is serialized, typically as a signed JSON Web Token (JWT), and sent to the PDP alongside the authentication request.
The evaluation phase occurs at the PDP, which parses the posture JWT and compares each attribute against the policy engine’s rule set. Modern implementations use Open Policy Agent (OPA) or similar policy-as-code frameworks, allowing security teams to express posture requirements in a declarative language. For example, a Rego policy for OPA might enforce that Windows endpoints must run build 22621 or later, have BitLocker enabled, and report a CrowdFalcon sensor version above 7.0.
Enforcement is handled by the policy enforcement point (PEP), which is typically the reverse proxy or identity-aware proxy sitting in front of application resources. The PEP receives the PDP’s decision and either forwards the request to the upstream application, redirects the user to a remediation portal, or returns an HTTP 403 with a machine-readable error payload that the endpoint agent can interpret to guide the user toward compliance.
Free to use, share it in your presentations, blogs, or learning materials.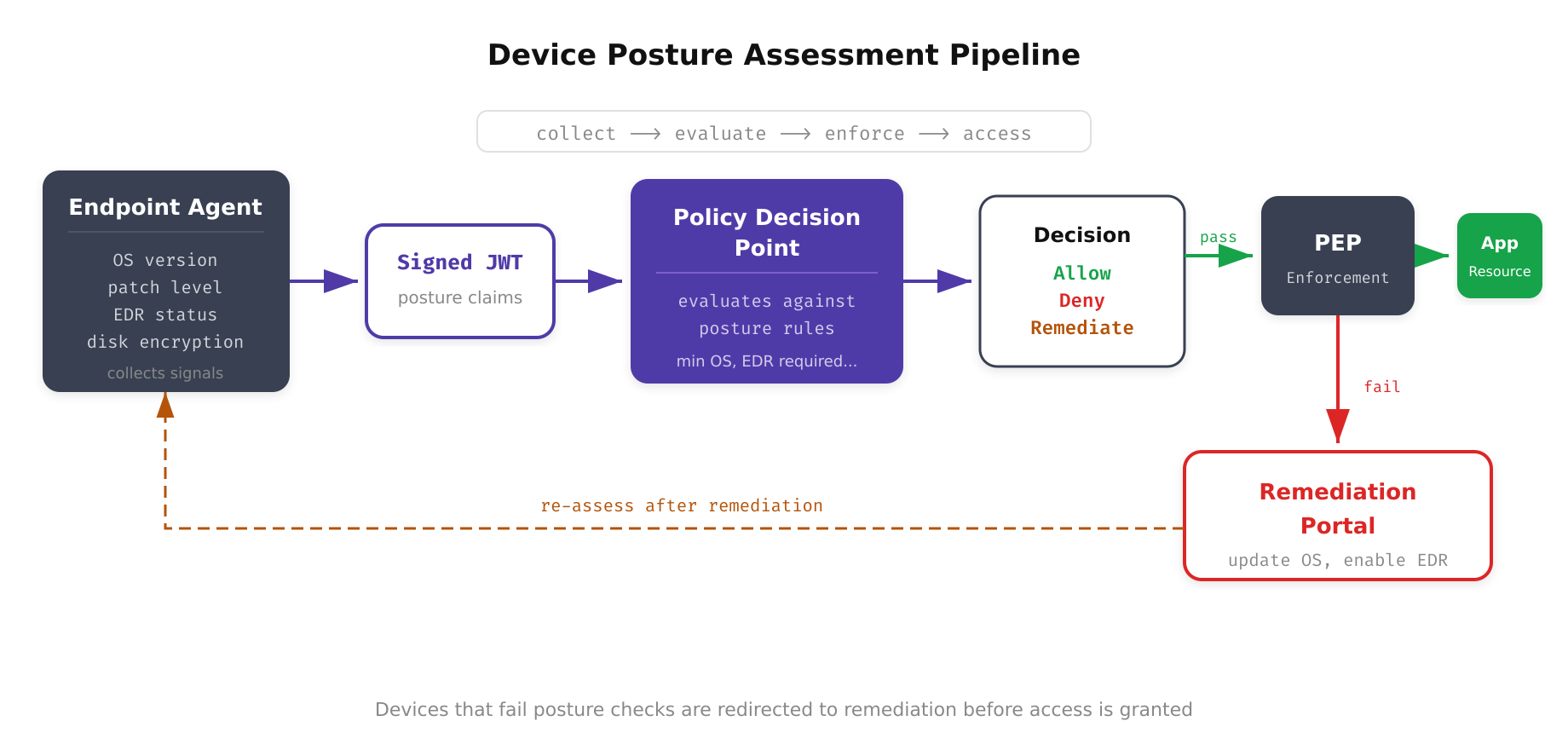
The above illustration maps the three-phase posture assessment pipeline from left to right. The endpoint agent collects device signals (OS version, patch level, EDR health, disk encryption), packages them into a signed JWT, and sends them to the Policy Decision Point. The PDP evaluates the signals against security policies and produces an allow, deny, or remediate decision. Non-compliant devices are redirected to a remediation portal rather than being permanently blocked.
Key Posture Signals and Their Implementation
Operating System and Patch Level
Querying the OS version is straightforward on most platforms. On Windows, the agent reads the CurrentBuildNumber from the registry at HKLMSOFTWAREMicrosoftWindows NTCurrentVersion. On macOS, sw_vers -productVersion returns the version string. On Linux, parsing /etc/os-release provides distribution and version information. Patch level verification is more nuanced. On Windows, the agent must enumerate installed KBs via WMI or the Windows Update Agent API, then compare them against a list of required patches maintained by the security operations team.
EDR Agent Presence and Health
Merely checking that an EDR process is running is insufficient. A sophisticated posture check verifies the agent’s version, confirms it is communicating with its cloud management console, checks the last policy update timestamp, and validates that real-time protection is active. CrowdStrike, SentinelOne, and Microsoft Defender for Endpoint each expose APIs or local health indicators that the posture agent can query. For CrowdStrike, the agent can check the Falcon sensor’s csagent.sys driver status and verify the sensor’s Registration Token File (RTF) is present and current.
Disk Encryption Status
On Windows, the agent invokes manage-bde -status or queries the Win32_EncryptableVolume WMI class to determine BitLocker status for each volume. On macOS, fdesetup status returns whether FileVault is on or off. On Linux, the agent checks for LUKS partitions by examining /proc/mounts and querying cryptsetup status for each mapped device. The posture policy should require encryption on all fixed drives, not just the boot volume.
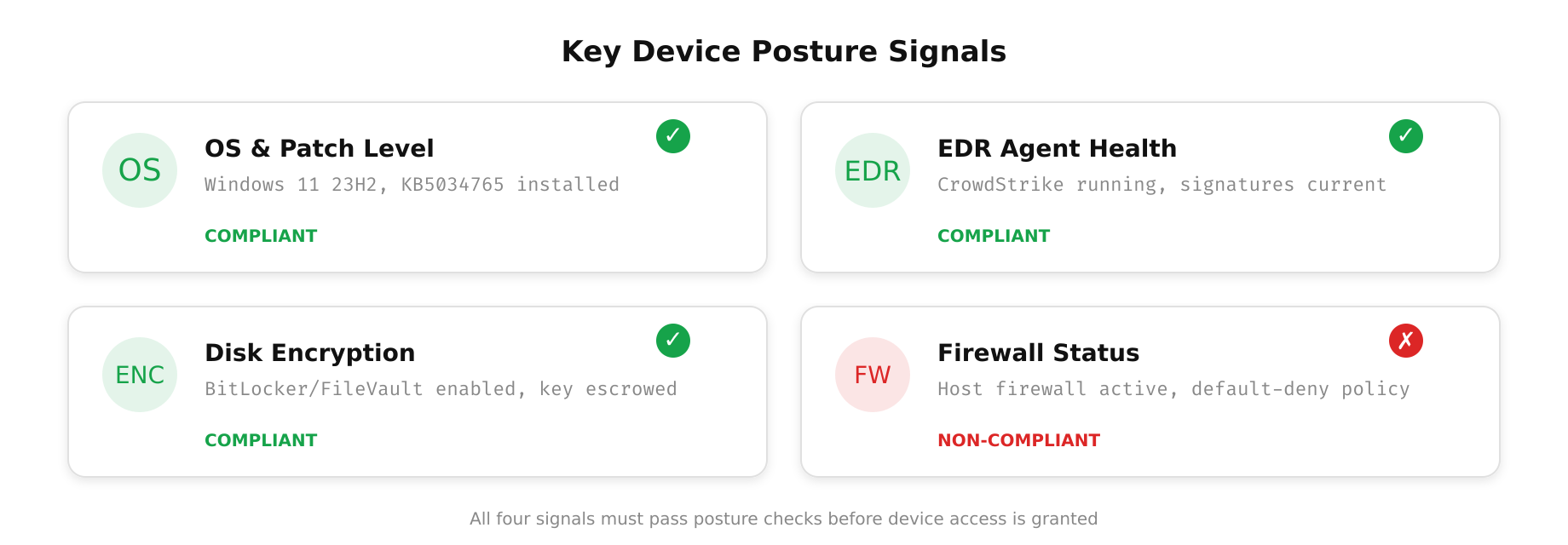
This diagram highlights the critical posture signals that endpoint agents collect and transmit to the Policy Decision Point. Each signal category, operating system version, patch compliance, disk encryption status, firewall configuration, EDR agent health, and certificate validity, represents a distinct compliance dimension that must be satisfied before access is granted under a Zero Trust policy.
Continuous Posture Evaluation
A single point-in-time posture check at authentication is necessary but not sufficient. Devices can become non-compliant during an active session: a user might disable their firewall, an EDR agent might crash, or a new vulnerability might be disclosed that changes the acceptable patch baseline. Continuous posture evaluation addresses this gap by periodically re-assessing the device throughout the session lifetime.
Implementation typically uses a heartbeat mechanism where the endpoint agent sends updated posture telemetry at configurable intervals, commonly every 60 to 300 seconds. The PDP re-evaluates the posture against the current policy set. If the device falls out of compliance, the PDP signals the PEP to terminate or downgrade the session. This can be implemented via short-lived access tokens with posture claims embedded in the JWT; when the token expires, the client must present fresh posture data to obtain a new token.
For latency-sensitive environments, a WebSocket channel between the agent and the PDP allows near-real-time posture updates. When the agent detects a state change, such as BitLocker being disabled or the EDR agent stopping, it immediately pushes an updated posture report. The PDP can then revoke the session within seconds rather than waiting for the next heartbeat interval.
Free to use, share it in your presentations, blogs, or learning materials.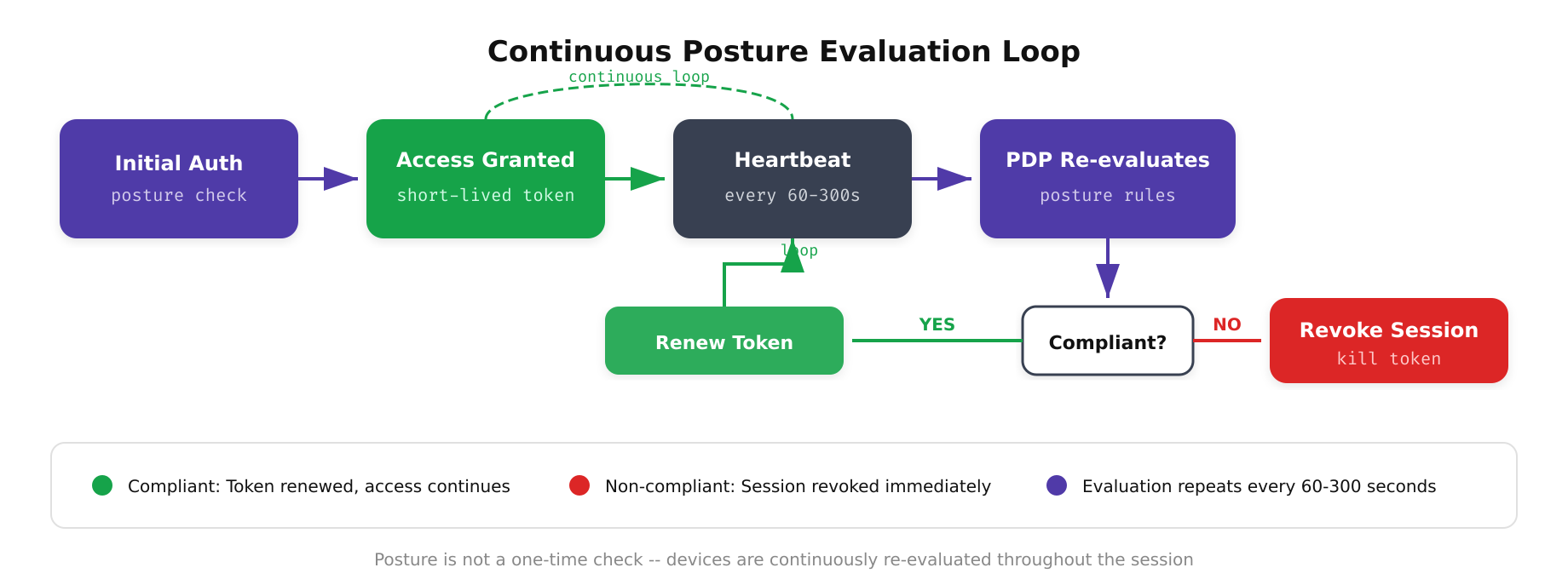
As shown above, the continuous posture assessment operates as a closed loop: the endpoint agent collects updated telemetry, the PDP evaluates it against the current policy set, the PEP enforces the resulting decision, and non-compliant devices are directed to remediation before re-entering the collection phase. This cyclical process ensures that device trust is never assumed to be static.
Deployment Strategies and Graduated Enforcement
Rolling out posture checks across an enterprise requires a phased approach to avoid disrupting productivity. A recommended strategy is to begin in audit-only mode, where posture data is collected and evaluated but access decisions are not enforced. This phase reveals the compliance landscape: what percentage of devices pass, which checks fail most frequently, and where remediation efforts should focus.
- Phase 1 – Audit Mode: Collect posture data across all endpoints. Generate compliance dashboards. Identify the top five failure reasons. Estimate remediation effort.
- Phase 2 – Soft Enforcement: Non-compliant devices receive warnings and are redirected to a self-service remediation portal, but access is not blocked. This trains users to maintain compliance.
- Phase 3 – Hard Enforcement on Sensitive Resources: Posture checks become mandatory for accessing high-value targets such as production infrastructure, financial systems, and PII datastores. Non-sensitive resources remain accessible to encourage adoption.
- Phase 4 – Full Enforcement: All corporate resources require a passing posture check. Emergency access procedures are documented for break-glass scenarios where a compliant device is unavailable.
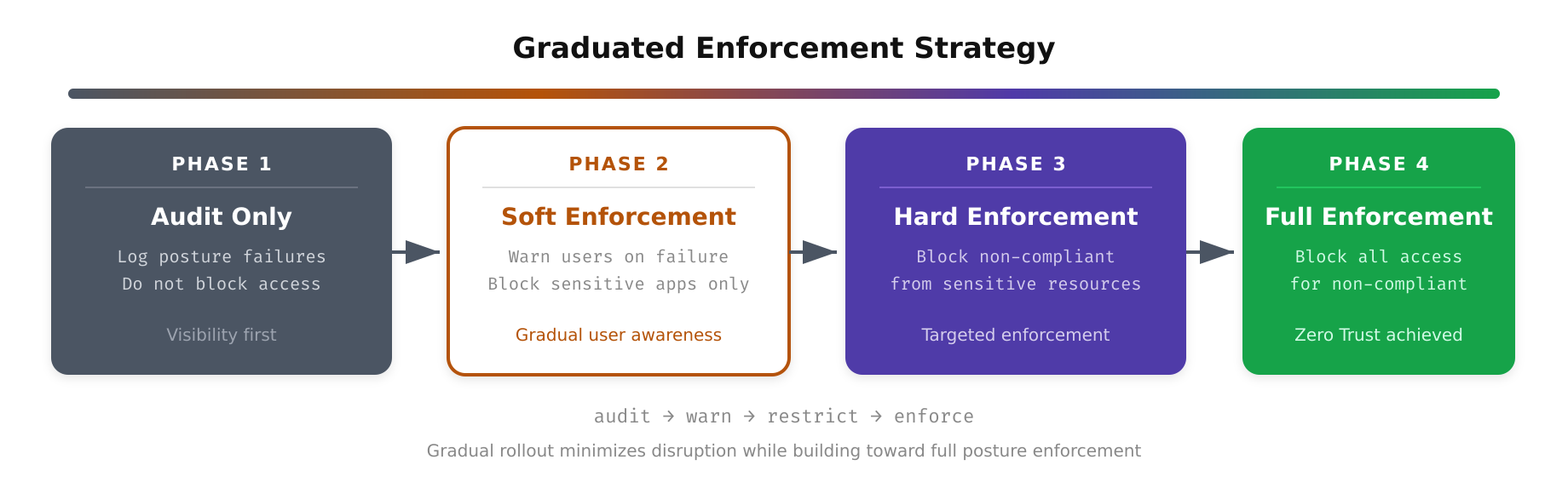
The above illustration depicts how enforcement actions are graduated based on the device’s posture score. Rather than a binary allow-or-deny outcome, the system applies tiered responses: fully compliant devices receive unrestricted access, partially compliant devices are limited to low-sensitivity resources, and devices that fail critical checks are quarantined and presented with step-by-step remediation instructions to restore compliance.
Challenges and Mitigation Approaches
Device posture checks introduce several operational challenges that must be addressed proactively. Agent deployment coverage is the most critical: if 15% of endpoints lack the posture agent, those devices represent a blind spot. MDM enrollment enforcement and conditional access policies that require agent presence before any authentication succeeds help close this gap.
Policy drift is another concern. As operating systems release updates and EDR vendors push new agent versions, the posture policy must be updated to reflect new acceptable baselines. Stale policies that reference outdated versions can either be too permissive, allowing known-vulnerable configurations, or too restrictive, blocking legitimately patched devices that moved beyond the specified version. Automating policy updates through integration with vendor release feeds and CVE databases reduces this risk.
Privacy considerations also arise, particularly in BYOD environments. Employees may resist posture agents that enumerate installed applications or inspect browser extensions on personal devices. A tiered approach, where personal devices undergo a minimal posture check such as OS version and encryption status while corporate-managed devices undergo full inspection, balances security with privacy expectations.
Device posture checks are a foundational pillar of Zero Trust endpoint security. When implemented with a well-architected collection, evaluation, and enforcement pipeline, they provide continuous assurance that every device accessing your resources meets your organization’s security baseline, shifting trust from the network perimeter to the individual endpoint.