The Identity Federation Challenge in Hybrid Cloud
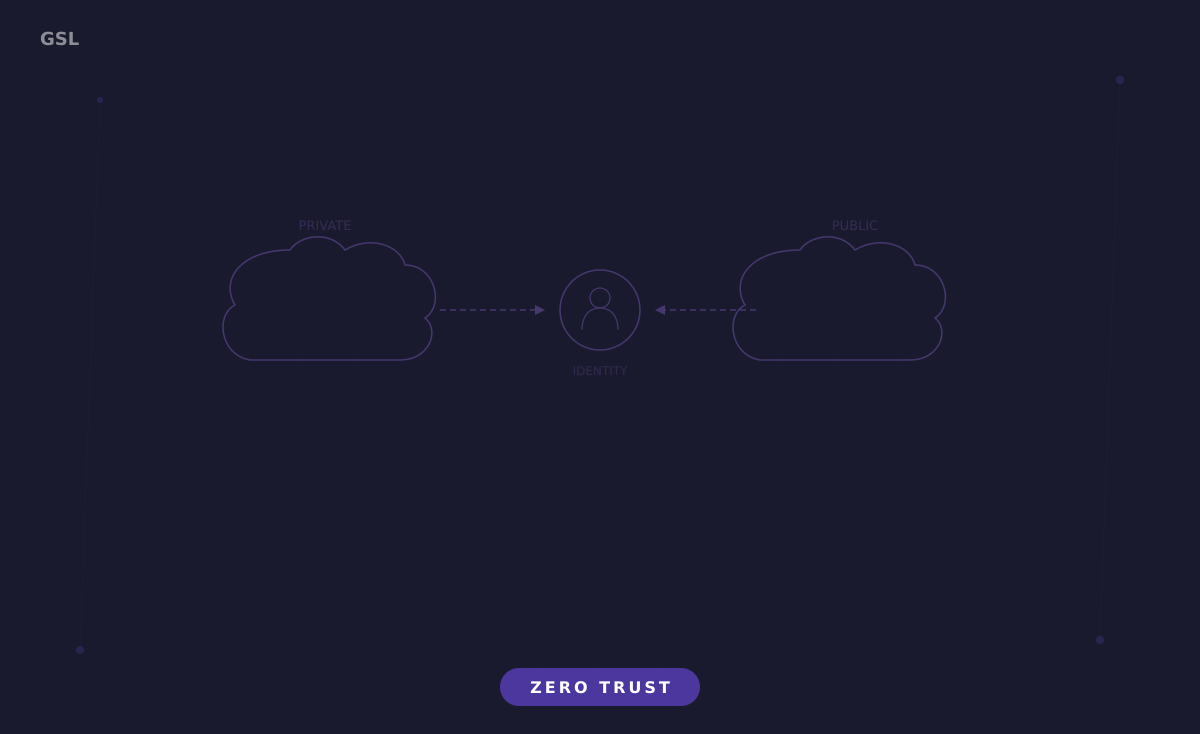
Hybrid cloud environments introduce a fundamental identity challenge that single-cloud deployments never face: a single user or workload needs authenticated access across on-premises Active Directory, cloud identity providers, SaaS applications, and partner systems, each with its own identity namespace, authentication protocols, and trust model. Without a coherent federation strategy, organizations end up with duplicate identities, inconsistent access policies, and gaps that attackers exploit to move laterally between environments.
Identity federation solves this by establishing trust relationships between identity providers (IdPs) so that a principal authenticated in one domain can access resources in another without creating a separate account. The protocols underlying federation (SAML 2.0, OpenID Connect, OAuth 2.0, and WS-Federation) each have specific strengths and use cases. Understanding when to use which protocol, and how to configure them securely, is the technical foundation of hybrid cloud Zero Trust.
Federation Protocols and Their Zero Trust Implications
SAML 2.0 remains the dominant protocol for enterprise SSO, particularly for web applications. In a SAML flow, the IdP issues a signed XML assertion containing the user’s identity attributes and group memberships. The Service Provider (SP) validates the assertion’s signature against the IdP’s public certificate, checks the assertion’s timestamps and audience restriction, and grants access based on the attributes. For Zero Trust, the critical configuration is ensuring that assertions include granular attributes (not just a username) that the SP can use for fine-grained authorization decisions: department, role, security clearance level, and device compliance status.
OpenID Connect (OIDC) is the modern alternative, built on OAuth 2.0 and using JSON Web Tokens (JWTs) instead of XML assertions. OIDC is the preferred protocol for cloud-native applications, API-based access, and mobile applications because JWTs are compact, easily validated, and natively supported by modern frameworks. Cloud providers have adopted OIDC as their workload federation standard: AWS STS AssumeRoleWithWebIdentity, GCP Workload Identity Federation, and Azure Workload Identity all use OIDC tokens for cross-platform authentication.
- SAML 2.0: Best for enterprise web SSO, supported by legacy applications, XML-based assertions with rich attribute support
- OpenID Connect: Best for cloud-native and API workloads, JWT-based tokens, simpler implementation than SAML
- OAuth 2.0: Delegated authorization (not authentication), used for API access scoping and consent
- SCIM 2.0: Not an authentication protocol, but essential for automated identity lifecycle provisioning across systems
Designing the Identity Architecture
The hub-and-spoke identity architecture places a single authoritative IdP at the center, with federation relationships radiating outward to cloud providers, SaaS applications, and partner organizations. For most enterprises, this hub is either on-premises Active Directory federated through AD FS, or a cloud-based IdP like Microsoft Entra ID, Okta, or Ping Identity. The hub IdP owns the user lifecycle: provisioning, attribute management, MFA enrollment, and deprovisioning. Spoke systems consume assertions from the hub and map them to local authorization models.
The critical design decision is where authentication policy enforcement occurs. In a Zero Trust model, the hub IdP should enforce authentication policies (MFA requirements, device compliance, risk-based step-up) before issuing any assertion or token. This ensures that regardless of which spoke system the user accesses, the same authentication baseline is applied. Spoke systems should then enforce authorization policies based on the attributes received in the token, not re-implement their own authentication logic.
For organizations with multiple on-premises Active Directory forests, Azure AD Connect or Okta AD Agent synchronizes identities to the cloud IdP. The synchronization should include only the attributes needed for access decisions, not the entire AD schema. Password hash synchronization (PHS) enables cloud-based authentication even when the on-premises AD is unreachable, providing resilience for hybrid scenarios. Pass-through authentication (PTA) validates passwords against on-premises AD in real time but introduces a dependency on network connectivity between the cloud IdP and the AD domain controller.
Cross-Cloud Workload Identity Federation
Workload identity federation between cloud providers eliminates the need for static credentials when services in one cloud need to access resources in another. Consider a data pipeline where an AWS Lambda function processes records and stores results in Google Cloud Storage. Without federation, you would create a GCP service account key, store it in AWS Secrets Manager, and rotate it periodically. With federation, the Lambda function’s IAM role presents its AWS credentials to GCP’s Workload Identity Pool, which exchanges them for a short-lived GCP access token scoped to the specific GCS bucket.
The trust configuration requires careful attribute mapping and condition enforcement. When configuring a GCP Workload Identity Provider for AWS, the provider validates that the incoming AWS STS token was issued by a specific AWS account and, optionally, that the assuming role matches a specific ARN pattern. Attribute conditions use Common Expression Language (CEL) to enforce constraints like assertion.arn.startsWith('arn:aws:sts::123456789012:assumed-role/production-'), ensuring that only production roles from the expected account can federate.
Azure Workload Identity Federation follows a similar pattern using federated identity credentials on Azure AD applications. A GitHub Actions workflow, for example, presents its OIDC token (issued by GitHub’s OIDC provider) to Azure AD, which validates the token’s issuer, subject (containing the repository and branch), and audience. Azure AD then issues an access token for the configured Azure resources. The subject claim filtering is critical: without it, any GitHub repository could potentially authenticate to your Azure subscription.
Token Security and Lifecycle Management
Tokens are the currency of federated identity, and their security is paramount. SAML assertions and JWTs must be signed with strong algorithms (RSA-2048 or ECDSA P-256 at minimum), and relying parties must validate signatures on every request rather than caching trust decisions. Token replay attacks are prevented through nonce validation, short expiration times (typically 5-15 minutes for SAML assertions, 1 hour for OIDC tokens), and audience restriction that ensures a token issued for one service cannot be replayed against another.
Certificate rotation for SAML signing certificates is a notoriously fragile process because every SP that trusts the IdP must update its copy of the public certificate before the rotation occurs. Automated certificate rollover, supported by IdPs like Entra ID and AD FS, publishes the new certificate in advance and signs assertions with the old certificate until the rollover date. Monitoring certificate expiration dates and testing rollover in pre-production environments prevents the catastrophic outage that occurs when an expired certificate breaks all federated sign-ins simultaneously.
- Set SAML assertion lifetime to the minimum acceptable value, typically 5 minutes for interactive flows
- Configure audience restriction on every SAML assertion and validate it at the SP
- Use asymmetric signing (RS256 or ES256) for JWTs; never use symmetric signing (HS256) in multi-party federation
- Implement certificate pinning or JWKS endpoint validation with caching and automatic refresh
- Monitor token issuance rates and alert on anomalous spikes that could indicate credential compromise
Operational Challenges and Best Practices
The operational complexity of hybrid identity federation scales with the number of trust relationships and the heterogeneity of the connected systems. A systematic approach to managing this complexity starts with an identity topology diagram that maps every federation relationship, the protocol used, the attributes exchanged, and the certificate expiration dates. This diagram must be maintained as a living document because a single broken trust relationship can cascade into widespread access failures.
Automated provisioning and deprovisioning through SCIM 2.0 is essential for maintaining Zero Trust in a federated environment. When an employee leaves the organization, their identity must be deactivated not just in the hub IdP but across every federated system that has provisioned a local account. SCIM automates this by propagating identity lifecycle events (create, update, disable, delete) from the hub IdP to connected SaaS applications. Without SCIM, orphaned accounts in federated systems become a persistent backdoor that bypasses Zero Trust controls.
Testing federation configurations requires a structured approach. Maintain a pre-production federation environment that mirrors production trust relationships. Test authentication flows from every entry point: direct IdP-initiated SSO, SP-initiated SSO, workload federation from each cloud provider, and emergency break-glass access paths. Load test the IdP to ensure it can handle peak authentication volumes without introducing latency that degrades user experience. Federation is infrastructure, and it demands the same rigor in testing, monitoring, and capacity planning as any other critical system.