Understanding Lateral Movement as the Primary Post-Breach Threat
Lateral movement is the technique by which an attacker, having compromised a single system, traverses the network to reach higher-value targets. It is not an exotic advanced persistent threat (APT) tactic; it is the standard operating procedure for virtually every serious breach. Ransomware operators compromise a single endpoint through phishing, then move laterally to reach domain controllers and file servers before encrypting the entire environment. Nation-state actors compromise a low-privilege web server, then pivot to database servers containing the data they are targeting. In the MITRE ATT&CK framework, lateral movement is an entire tactic category (TA0008) with over a dozen documented techniques.
The reason lateral movement is so effective is that traditional networks are designed for it. Flat network architectures, shared credentials, overly permissive firewall rules, and lack of internal monitoring create an environment where moving from one compromised system to the next requires minimal effort. Preventing lateral movement requires systematically eliminating the conditions that enable it, and this is where Zero Trust architecture provides its greatest value.
How Attackers Move Laterally: Technical Mechanics
To prevent lateral movement, you must understand the specific techniques attackers use. The most common techniques in enterprise environments are well-documented and predictable.
Credential-Based Lateral Movement
The most common lateral movement technique is credential theft and reuse. An attacker compromises a workstation, dumps cached credentials from memory using tools like Mimikatz, and uses those credentials to authenticate to other systems. On Windows networks, this takes several forms: Pass-the-Hash (PtH) uses captured NTLM hashes to authenticate without knowing the plaintext password. Pass-the-Ticket (PtT) uses stolen Kerberos tickets (TGTs or service tickets) to impersonate the compromised user. Overpass-the-Hash converts an NTLM hash into a Kerberos ticket. Golden Ticket attacks use a compromised KRBTGT hash to forge arbitrary Kerberos tickets.
On Linux systems, attackers steal SSH private keys from ~/.ssh/ directories, extract credentials from environment variables, configuration files, or secrets management caches, and reuse session tokens from running applications.
Protocol-Based Lateral Movement
Attackers exploit legitimate administrative protocols to move between systems. Remote Desktop Protocol (RDP) provides full graphical access to Windows systems. Server Message Block (SMB) enables file access and remote service execution through tools like PsExec. Windows Management Instrumentation (WMI) allows remote command execution. SSH provides remote shell access on Linux and Unix systems. PowerShell Remoting (WinRM) enables remote script execution on Windows. Each of these protocols is legitimate and necessary for administration. The problem is that they are typically available from any internal network location to any internal server, with no access controls beyond credential authentication.
Exploitation-Based Lateral Movement
When credentials are not available, attackers exploit vulnerabilities in network services to gain access to adjacent systems. Unpatched SMB services (EternalBlue), vulnerable web applications on internal servers, and exploitable database services provide direct code execution without requiring credentials. Internal services are often less rigorously patched than internet-facing services because they are considered “protected” by the perimeter, a dangerous assumption that Zero Trust explicitly rejects.
Free to use, share it in your presentations, blogs, or learning materials.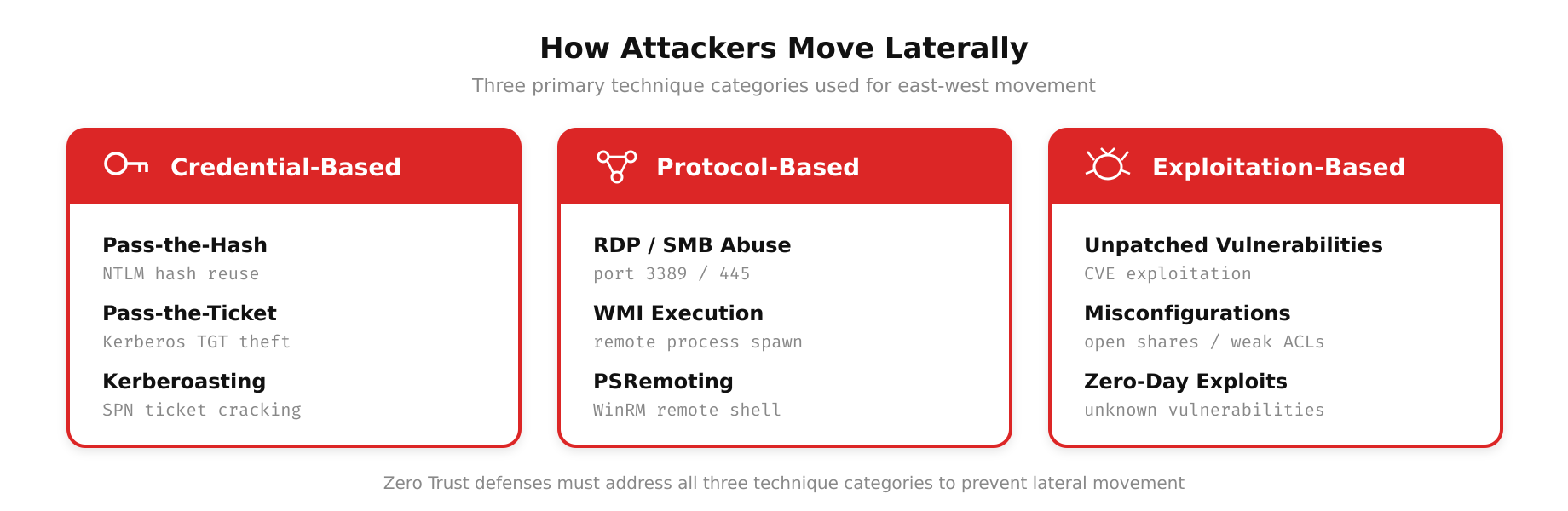
This diagram highlights the primary lateral movement techniques attackers employ after an initial compromise. From credential-based methods such as pass-the-hash, credential dumping, and Kerberos ticket theft, through protocol-based pivoting via RDP, SMB, and WinRM, to exploitation-based movement targeting unpatched internal services, each vector represents a distinct path that must be addressed in a layered defense strategy.
Free to use, share it in your presentations, blogs, or learning materials.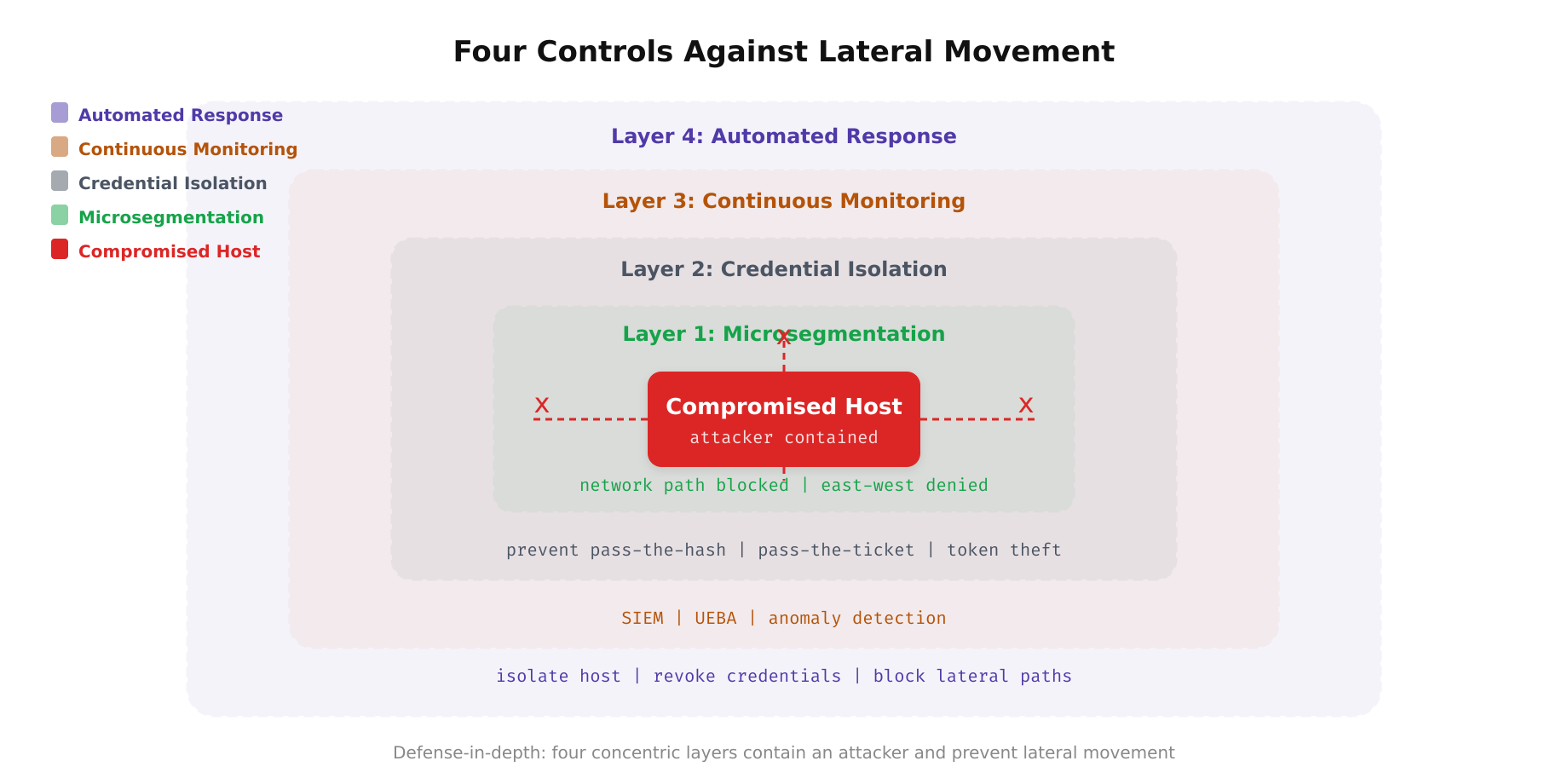
The above illustration visualizes the defense-in-depth strategy against lateral movement. When an attacker compromises a host, four concentric layers of control work to contain the breach. Microsegmentation restricts available network paths, credential isolation prevents pass-the-hash and ticket attacks, continuous monitoring detects anomalous movement patterns, and automated response isolates the host and revokes compromised credentials.
Control 1: Microsegmentation to Restrict Network Paths
The first line of defense against lateral movement is ensuring that compromised workloads cannot reach targets they have no legitimate reason to communicate with. Microsegmentation restricts east-west traffic to only the flows required by the application architecture.
In practice, this means that developer workstations cannot directly communicate with production databases. Application servers can reach only the specific database instances their application uses, not every database in the data center. Management protocols (RDP, SSH, WinRM) are restricted to connections from designated jump hosts or privileged access workstations, not from arbitrary endpoints. Inter-segment traffic that is permitted is logged and monitored for anomalous patterns.
The effectiveness of microsegmentation against lateral movement depends on granularity. Segmenting production from development stops cross-environment movement but does not prevent lateral movement within production. Segmenting by application tier (web, app, database) adds another barrier. Segmenting individual services within tiers provides the strongest containment but requires the most operational effort to manage policies.
Free to use, share it in your presentations, blogs, or learning materials.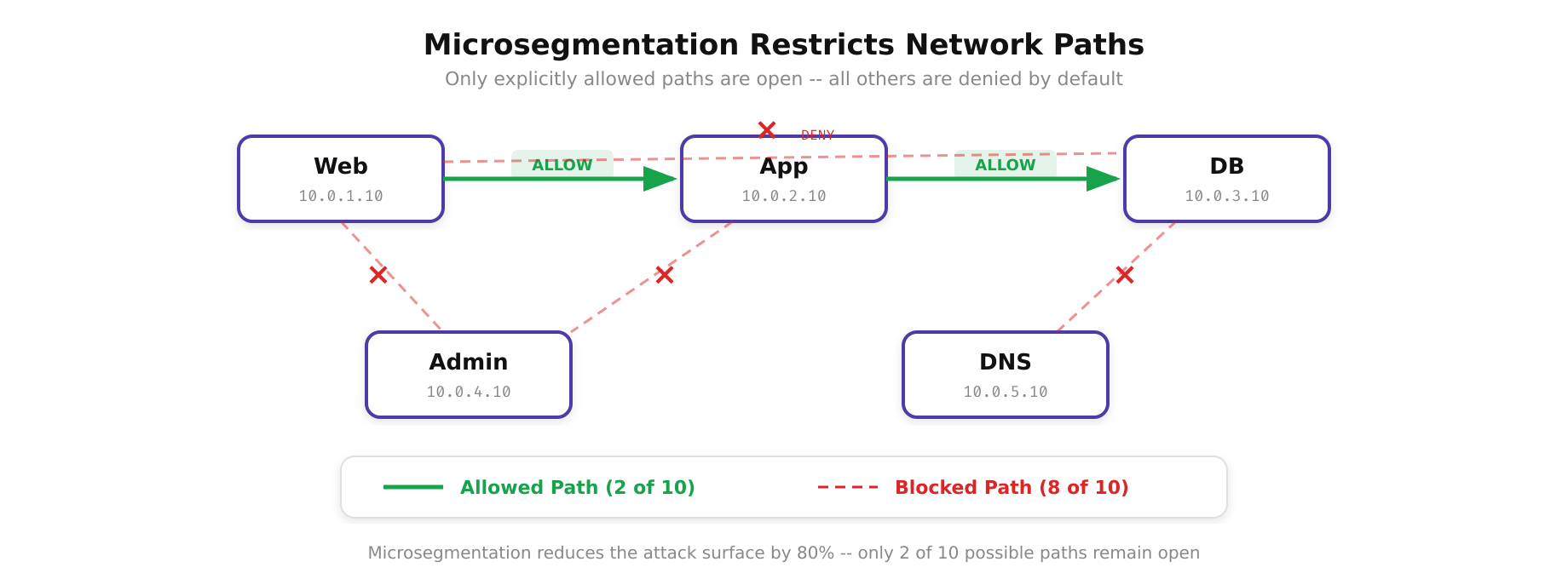
As shown above, the contrast between a flat network and a microsegmented network is stark. In the flat network, an attacker who compromises any single node can reach every other node through unrestricted lateral paths. In the microsegmented architecture, each workload communicates only through explicitly permitted corridors, transforming the network into a series of isolated zones where lateral movement is blocked by default.
Control 2: Credential Isolation and Privileged Access Management
If microsegmentation restricts where an attacker can go, credential isolation restricts who they can become. The goal is to ensure that credentials captured on one system are useless on other systems.
- Tiered administration: Implement a tiered credential model where Tier 0 credentials (domain admins, enterprise admins) are used only on Tier 0 systems (domain controllers). Tier 1 credentials (server admins) are used only on servers. Tier 2 credentials (workstation admins) are used only on workstations. A Tier 0 credential never touches a workstation, so compromising a workstation cannot yield domain admin access.
- Local Administrator Password Solution (LAPS): Ensure every workstation and server has a unique local administrator password. LAPS (or its open-source alternative) generates random, unique passwords for each machine’s local admin account and stores them in Active Directory with controlled read access. An attacker who captures the local admin password on one workstation cannot use it on any other workstation.
- Ephemeral credentials: Replace long-lived credentials with short-lived, just-in-time credentials. For SSH access, use certificate-based authentication with certificates that expire in 8-12 hours, issued through a tool like HashiCorp Vault or Teleport. For database access, generate temporary credentials that are revoked automatically. For cloud console access, use federated identity with session duration limits.
- Credential Guard and protected process: On Windows, enable Credential Guard to isolate LSASS (Local Security Authority Subsystem Service) in a virtualization-based security enclave. This prevents Mimikatz and similar tools from dumping credentials from memory, eliminating the most common credential theft technique.
Control 3: Continuous Monitoring and Anomaly Detection
Even with microsegmentation and credential isolation, determined attackers may find paths through your defenses. Continuous monitoring provides the detection layer that catches lateral movement attempts in progress.
Key telemetry sources for lateral movement detection include Windows Event Logs, specifically Event IDs 4624 (successful logon) and 4625 (failed logon) with logon type analysis. Logon type 3 (network logon) from an unexpected source, logon type 10 (RDP) to a server that does not normally receive RDP connections, or a burst of type 3 logons across multiple servers from a single source are strong indicators of lateral movement.
Network flow data reveals communication patterns that deviate from the established baseline. A workstation that suddenly begins connecting to dozens of servers on SMB port 445 is likely running a credential spraying or share enumeration attack. A server in the web tier that initiates outbound connections to the database tier on a port it has never used before warrants immediate investigation.
EDR telemetry provides process-level visibility. The execution of tools like Mimikatz, PsExec, WMIexec, or their renamed variants should trigger immediate alerts. More subtle indicators include unusual parent-child process relationships (cmd.exe spawning from Excel.exe), LSASS memory access from non-standard processes, and service installation on remote systems.
Control 4: Automated Response and Containment
Detection without response is observation without action. When lateral movement is detected, automated containment procedures must execute faster than the attacker can move to the next target.
- Automated network isolation: When a host is confirmed compromised, automatically move it to a quarantine VLAN or update microsegmentation policies to block all traffic from the host except connectivity to the forensic analysis subnet. This must execute in seconds, not minutes.
- Credential revocation: Automatically disable the compromised user’s account in the identity provider, revoke all active sessions across SSO-connected applications, and rotate credentials for any service accounts that were accessible from the compromised host.
- Blast radius assessment: Automatically identify all systems the compromised host communicated with during the incident window and add them to the investigation queue. Check whether those systems show indicators of compromise (IoCs) from the same attack tooling.
- Kerberos ticket invalidation: If credential theft is suspected, reset the compromised user’s password and the KRBTGT account password (twice, to invalidate all outstanding tickets). This is a disruptive operation that requires a maintenance window but is necessary to eliminate stolen Kerberos tickets.
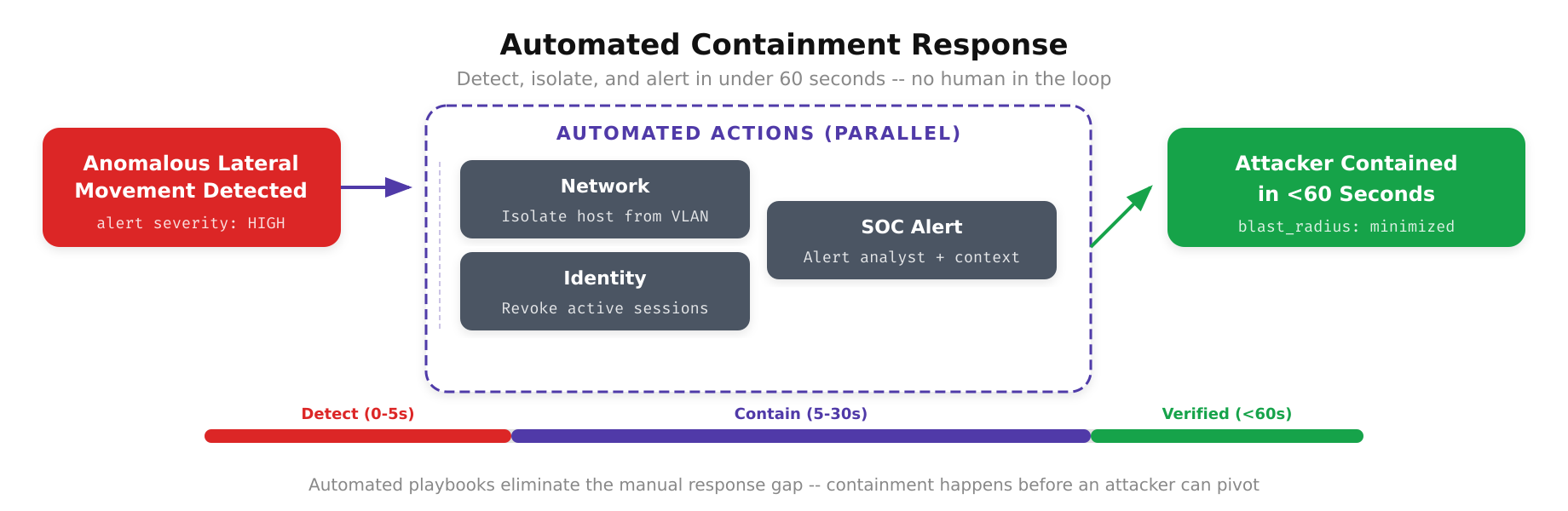
The above illustration depicts the automated containment workflow that activates the moment lateral movement is detected. From the initial detection trigger, the system launches parallel response actions, isolating the compromised host on a quarantine VLAN, revoking all associated credentials and active sessions, assessing the blast radius by tracing communication paths, and capturing forensic evidence for investigation. This orchestrated response executes in seconds, closing the window of opportunity before the attacker can pivot further.
Preventing lateral movement is not a single technology deployment. It is a layered defense strategy that combines network segmentation to limit where attackers can go, credential isolation to limit who they can impersonate, monitoring to detect movement attempts, and automated response to contain compromises before they spread. Each layer independently reduces the attacker’s capability, and together they transform the network from an open playing field into a series of dead ends. This is what Zero Trust delivers in practice: not the prevention of initial compromise, but the containment of its impact.
