Cutting Through the Buzzword: Defining Zero Trust
Zero Trust has become one of the most overused terms in cybersecurity. Vendors slap it on products, executives demand it in board meetings, and engineers are left trying to figure out what it actually means in practice. At its core, Zero Trust is an architectural philosophy: no entity, whether inside or outside the network perimeter, is inherently trusted. Every access request must be authenticated, authorized, and continuously validated before granting access to resources.
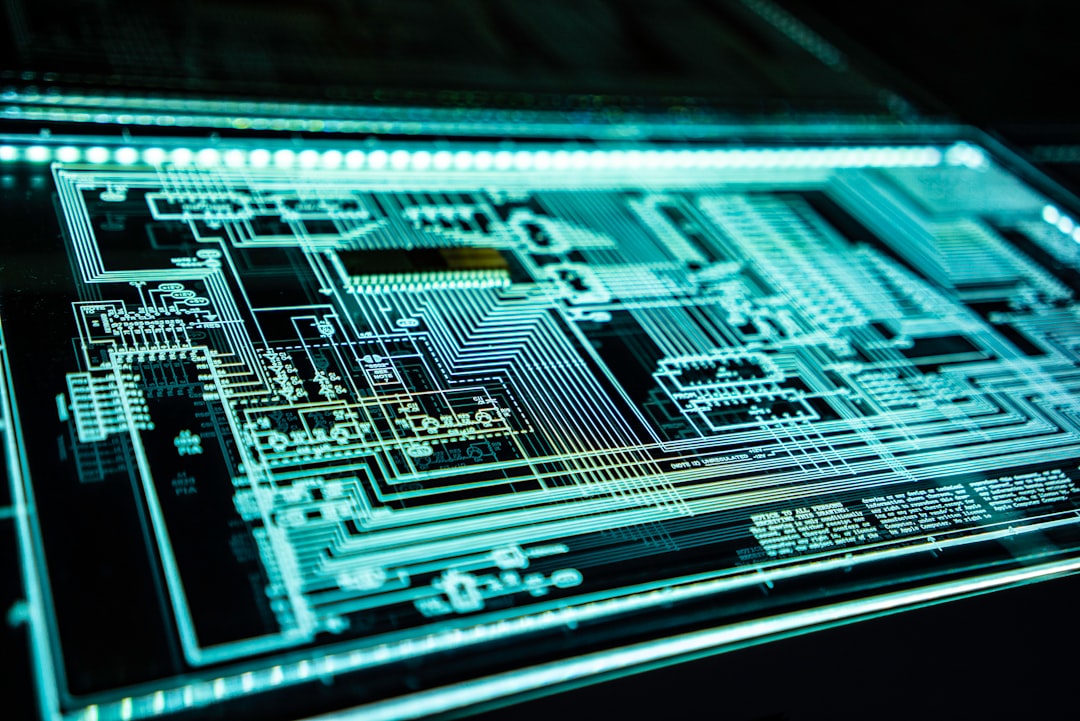
The term was coined by John Kindervag at Forrester Research in 2010, but the underlying principles predate the label. The concept emerged from a simple observation: traditional perimeter-based security assumes that everything inside the network is trustworthy. This assumption has been catastrophically wrong in breach after breach, from the Target compromise in 2013 to the SolarWinds supply chain attack in 2020.
Zero Trust is not a product you purchase. It is not a single technology. It is a strategic approach to security architecture that fundamentally changes how organizations think about access control, network segmentation, and identity verification.
Free to use, share it in your presentations, blogs, or learning materials.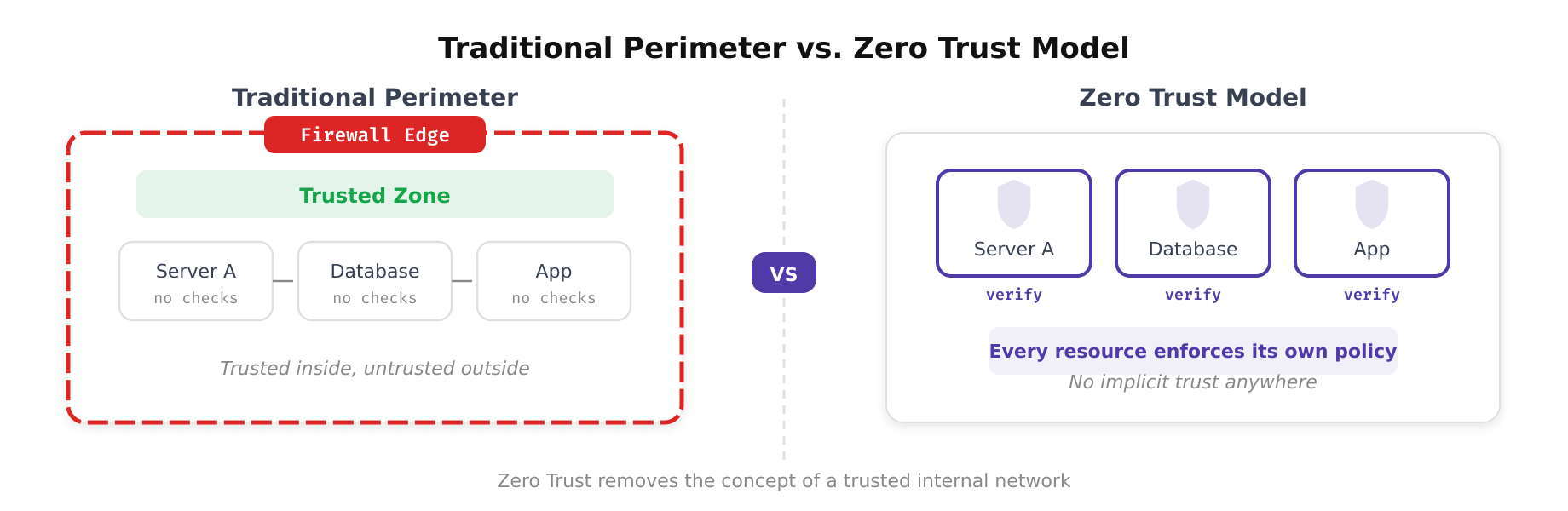
The above illustration depicts the fundamental contrast between traditional perimeter-based security and Zero Trust architecture. On the left, a single firewall boundary separates trusted internal resources from the outside world. On the right, Zero Trust enforces identity-based verification at every access point, eliminating the concept of an inherently trusted zone.
What Zero Trust Actually Is
Zero Trust operates on a set of foundational assumptions that reshape security design decisions. Understanding these assumptions is critical for any engineer tasked with implementing or evaluating a Zero Trust architecture.
- Assume breach: Design every system as if an attacker already has a foothold in your environment. This forces you to implement controls that limit lateral movement, even within trusted network segments.
- Verify explicitly: Every access request must be authenticated and authorized based on all available data points, including user identity, device health, location, service or workload context, data classification, and anomalies in behavior.
- Least privilege access: Users and services receive only the minimum permissions necessary to perform their function, enforced through just-in-time and just-enough-access policies.
- Microsegmentation: Network segments are broken into granular zones, and traffic between zones is inspected and controlled regardless of whether the source and destination are both internal.
In practical terms, this means that a database server in your data center does not automatically trust a request from an application server sitting on the same VLAN. The application server must present valid credentials, its device posture must be verified, and the request must conform to predefined access policies before the database responds.
What Zero Trust Is Not
Misunderstanding what Zero Trust is not may be even more important than understanding what it is. The market is saturated with misleading claims, and engineers need to be equipped to cut through the noise.
It Is Not a Product
No single vendor solution delivers Zero Trust out of the box. When a vendor tells you their next-generation firewall “is Zero Trust,” they are selling you a component that may contribute to a Zero Trust architecture, but the firewall alone is not the architecture. Zero Trust requires orchestration across identity providers, endpoint detection and response (EDR) platforms, network access controls, security information and event management (SIEM) systems, and policy engines. It is a design pattern, not a SKU.
It Is Not About Eliminating Trust Entirely
The name is slightly misleading. Zero Trust does not mean that trust never exists. It means that trust is never implicit. Trust is established dynamically through continuous verification. A user who authenticates with a hardware security key from a managed device on a known network may be granted broader access than the same user authenticating with a password from an unmanaged device on a public Wi-Fi network. Trust exists; it is simply earned and re-evaluated continuously.
It Is Not a Rip-and-Replace Strategy
Zero Trust is not an all-or-nothing proposition. Organizations do not need to discard their existing infrastructure and start from scratch. The most successful Zero Trust implementations are incremental, starting with the highest-risk assets and expanding outward. Google’s BeyondCorp initiative, one of the earliest large-scale Zero Trust implementations, took years to fully deploy and evolved continuously based on operational feedback.
Free to use, share it in your presentations, blogs, or learning materials.
This diagram highlights the most persistent misconceptions surrounding Zero Trust. It clarifies that Zero Trust is not a product you can buy off the shelf, not merely multi-factor authentication, not a one-time implementation project, and not a philosophy rooted in organizational distrust, it is a continuous architectural discipline.
The Architecture in Practice
A functional Zero Trust architecture consists of several interacting components. The NIST Special Publication 800-207 provides a reference architecture that includes a Policy Engine (PE), a Policy Administrator (PA), and a Policy Enforcement Point (PEP). Here is how these components interact in a real-world scenario.
Consider an engineer attempting to SSH into a production server. In a traditional model, the engineer connects to the corporate VPN, and once on the internal network, accesses the server directly. In a Zero Trust model, the flow looks different:
- The engineer initiates an access request through a Zero Trust proxy or gateway (the PEP).
- The PEP queries the Policy Engine, which evaluates the request against predefined policies. Is the user authenticated via MFA? Is the device running an approved OS version with up-to-date patches? Is the request coming during normal working hours? Does the user have an active access grant for this specific server?
- The Policy Engine returns a decision to the Policy Administrator, which instructs the PEP to either allow or deny the connection.
- If allowed, the session is established, but it is continuously monitored. If the device posture changes mid-session (for example, the EDR agent detects malware), the Policy Engine can revoke the session in real time.
This architecture eliminates the concept of a trusted network zone. The engineer could be sitting in the office, at home, or in a coffee shop. The access decision is identical because it is based on identity and context, not network location.
Free to use, share it in your presentations, blogs, or learning materials.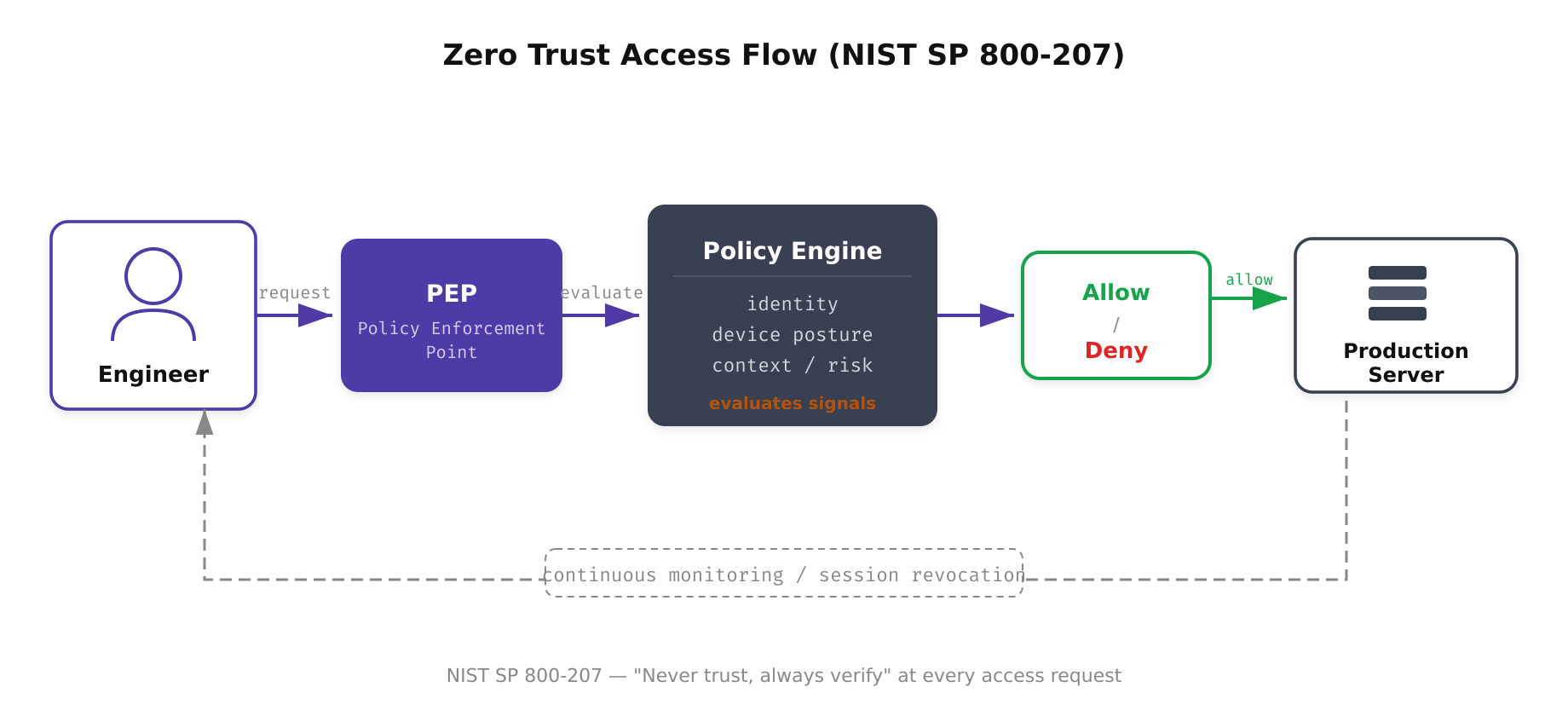
The above illustration shows how every access request in a Zero Trust environment flows through the Policy Enforcement Point and Policy Engine before reaching the target resource. The continuous monitoring feedback loop ensures trust is re-evaluated throughout the session, not just at the initial connection.
Where Organizations Go Wrong
The most common failure mode in Zero Trust adoption is treating it as a technology project rather than an architectural shift. Organizations purchase a Zero Trust Network Access (ZTNA) product, deploy it for remote access, and declare victory. But if the internal network still operates on implicit trust, if service accounts have standing privileges that are never rotated, if east-west traffic flows uninspected between workloads, then the organization has not adopted Zero Trust. It has deployed a VPN replacement.
Another frequent mistake is neglecting identity as the foundation. Zero Trust begins with strong identity. If your identity provider lacks multi-factor authentication, if service accounts share credentials, or if your directory contains thousands of stale accounts with active permissions, no amount of network segmentation will compensate. Identity is the new perimeter, and it must be treated with the same rigor that organizations once applied to firewalls.
A third pitfall is ignoring data classification. Zero Trust policies are most effective when they are context-aware, and data classification provides critical context. An access request to a development environment with synthetic data should be treated differently than an access request to a production database containing customer financial records. Without data classification, policy engines lack the information needed to make nuanced access decisions.
Free to use, share it in your presentations, blogs, or learning materials.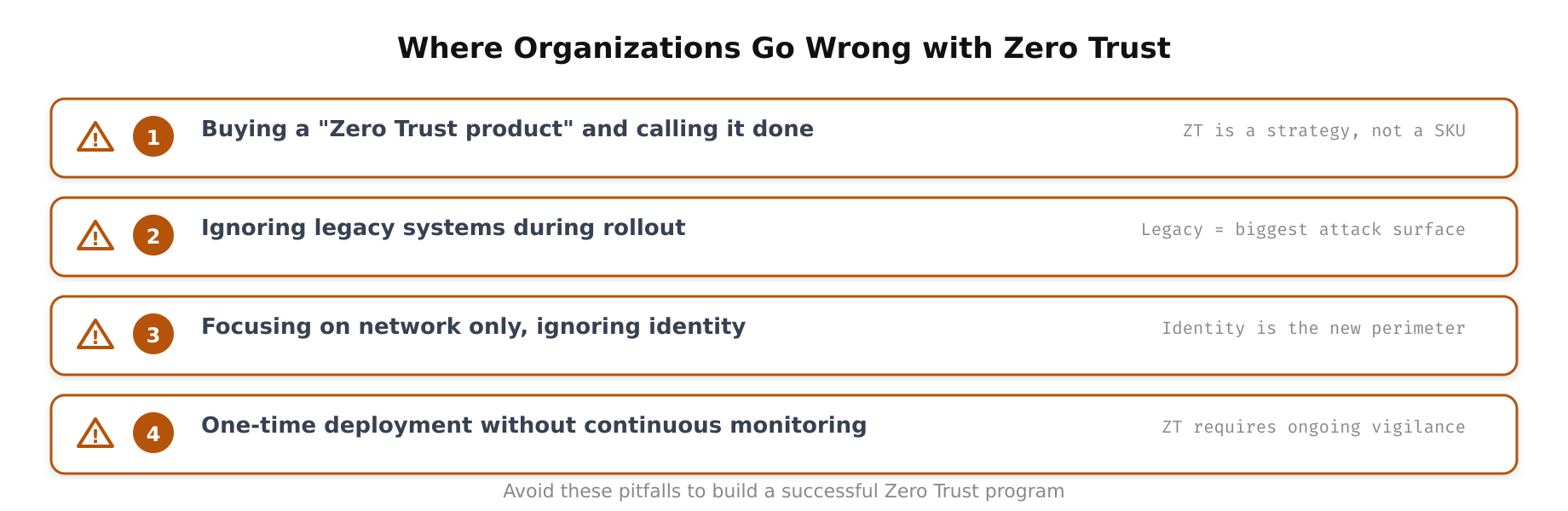
As shown above, the most frequent pitfalls in Zero Trust adoption stem from treating it as a technology purchase rather than an architectural transformation. The diagram maps out how over-reliance on vendors, neglecting identity foundations, and ignoring data classification each undermine the effectiveness of a Zero Trust strategy.
The Bottom Line for Engineers
Zero Trust is a design philosophy that eliminates implicit trust from your architecture. It is implemented through a combination of strong identity verification, device posture assessment, microsegmentation, least-privilege access, and continuous monitoring. It is not a product, not a quick fix, and not something you can achieve by deploying a single tool.
For engineers evaluating Zero Trust, the questions to ask are straightforward: Does every access request in your environment require explicit authentication and authorization? Can you enforce least privilege at the application, network, and data layers? Can you detect and respond to anomalies in real time? If the answer to any of these is no, that is where your Zero Trust journey begins.
The goal is not perfection on day one. The goal is incremental, measurable progress toward an architecture where trust is never assumed and always verified.