What Is Continuous Authentication?
Traditional authentication models operate on a simple binary assumption: once a user proves their identity at the login gate, they are trusted for the duration of the session. This model is fundamentally broken in a Zero Trust architecture. Continuous authentication replaces the one-time checkpoint with an ongoing verification loop that re-evaluates the legitimacy of every session in real time, using signals that extend far beyond passwords and tokens.
In practice, continuous authentication means that a user who authenticates at 09:00 may have their trust posture re-assessed at 09:01, 09:05, and every meaningful event in between. The system ingests behavioral biometrics, device health telemetry, network context, and resource sensitivity to produce a living trust score. When that score degrades below a threshold, the system can step up authentication, restrict access scope, or terminate the session entirely.
Free to use, share it in your presentations, blogs, or learning materials.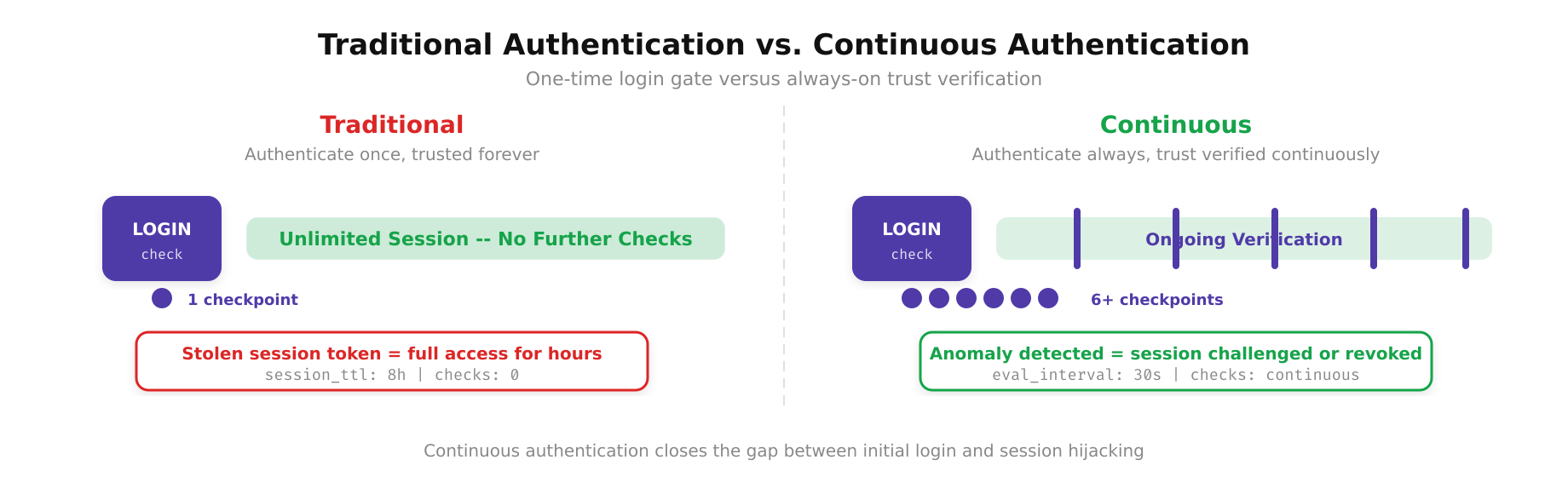
The above illustration depicts the fundamental difference between traditional and continuous authentication models. On the left, the traditional approach authenticates the user once at the gate and then trusts the session unconditionally until expiry. On the right, continuous authentication maintains an active trust evaluation loop, every request, every context change, and every behavioral signal is assessed in real time, ensuring that trust is never assumed but always verified.
The Signal Pipeline: From Raw Events to Trust Decisions
Continuous authentication depends on a robust signal pipeline. Signals are collected from multiple layers of the stack and funneled into a policy decision point (PDP) that evaluates trust in near real time. The quality and diversity of these signals directly determine the accuracy of the trust assessment.
Device-Level Signals
- Endpoint Detection and Response (EDR) agent status: whether the agent is running, its last check-in time, and any active detections.
- OS patch level and configuration compliance against a CIS benchmark baseline.
- Disk encryption state (BitLocker, FileVault, LUKS) verified through MDM attestation.
- Certificate validity on the device, including client TLS certificates used for mTLS connections.
User Behavioral Signals
- Keystroke dynamics and mouse movement patterns (passive biometrics that do not interrupt the user).
- Session activity patterns: frequency of API calls, accessed resources, and time-of-day deviations from historical norms.
- Geolocation and impossible travel detection using IP geolocation databases and VPN exit node mapping.
- Privilege escalation attempts or access to resources outside the user’s baseline profile.
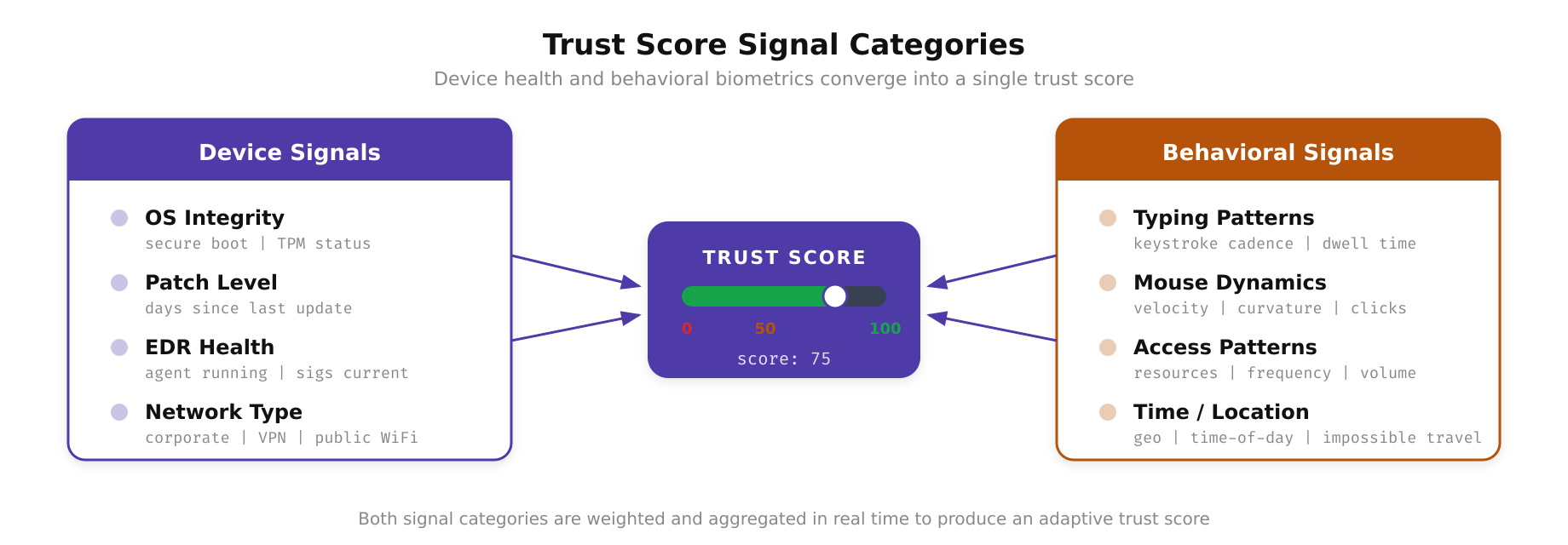
This diagram highlights the diverse signal categories that feed into the continuous trust score calculation. Device posture checks verify endpoint compliance, geolocation and network context detect environmental anomalies, behavioral biometrics track interaction patterns, and time-of-access analysis identifies deviations from established usage norms. Each signal carries a weighted contribution, and their combined assessment produces the dynamic trust score that determines whether a session continues, faces a challenge, or is terminated.
Free to use, share it in your presentations, blogs, or learning materials.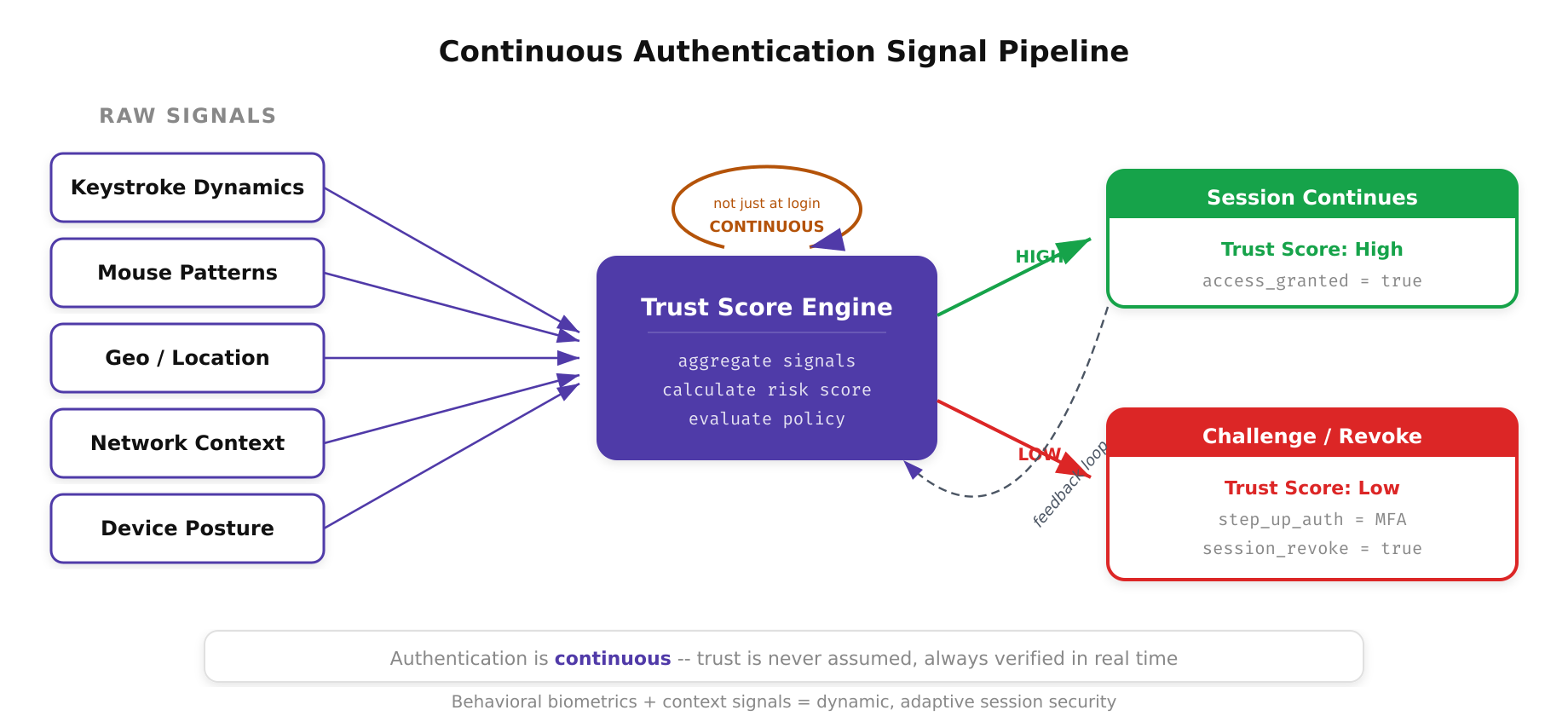
The above illustration traces the continuous authentication signal pipeline from end to end. Raw behavioral and device signals, keystroke dynamics, mouse patterns, location, network context, and device posture, feed continuously into the Trust Score Engine. Rather than authenticating once at login, the engine recalculates trust in real time. A high trust score allows the session to continue uninterrupted, while a drop in trust triggers a step-up authentication challenge or session revocation.
Architecture of a Continuous Authentication System
A production-grade continuous authentication system typically follows a three-tier architecture: signal collection, trust evaluation, and enforcement. Each tier must be designed for low latency and high availability because any delay in the evaluation pipeline directly impacts user experience and security posture.
At the signal collection tier, lightweight agents and proxies stream events to a centralized event bus. In most implementations, this is Apache Kafka or a managed equivalent such as Amazon Kinesis or Azure Event Hubs. Events are serialized in a compact format (Protocol Buffers or Avro) and partitioned by session identifier to ensure ordered processing per user session.
The trust evaluation tier consumes these events through a stream processing engine such as Apache Flink or Kafka Streams. The engine applies a scoring model that weights each signal according to the resource’s sensitivity classification. For instance, accessing an internal wiki might tolerate a device with a slightly outdated patch level, while accessing the production Kubernetes API server demands a fully compliant device and recent MFA verification. The scoring model outputs a numeric trust score between 0 and 100, which maps to predefined policy tiers.
The enforcement tier intercepts requests at the policy enforcement point (PEP), typically a reverse proxy or service mesh sidecar. When the PDP signals that a session’s trust has degraded, the PEP can inject an authentication step-up challenge (FIDO2 prompt, push notification), reduce the session’s OAuth scope in real time, or drop the connection entirely. This separation of decision and enforcement is critical for maintaining a clean architecture that can evolve independently at each tier.
Step-Up Authentication and Adaptive Challenges
One of the most practical outcomes of continuous authentication is step-up authentication. Rather than immediately terminating a suspicious session, the system can request additional proof of identity proportional to the risk detected. This preserves productivity while mitigating risk.
Consider a scenario where an engineer is working from their usual office IP, on a compliant laptop, during normal business hours. Their trust score sits at 92. They then initiate a VPN connection that changes their egress IP to a residential address in a different city. The trust score drops to 65. The system does not terminate the session. Instead, it prompts for a FIDO2 hardware key verification. Once the engineer taps the key, the score recovers to 85, and the session continues with full access.
Now consider a second scenario. The same engineer’s session begins exhibiting rapid-fire API calls to endpoints they have never accessed before, from a device whose EDR agent stopped reporting 20 minutes ago. The trust score drops to 30. In this case, the system terminates the session, revokes the OAuth tokens, and triggers an automated incident workflow that notifies the security operations team.
Free to use, share it in your presentations, blogs, or learning materials.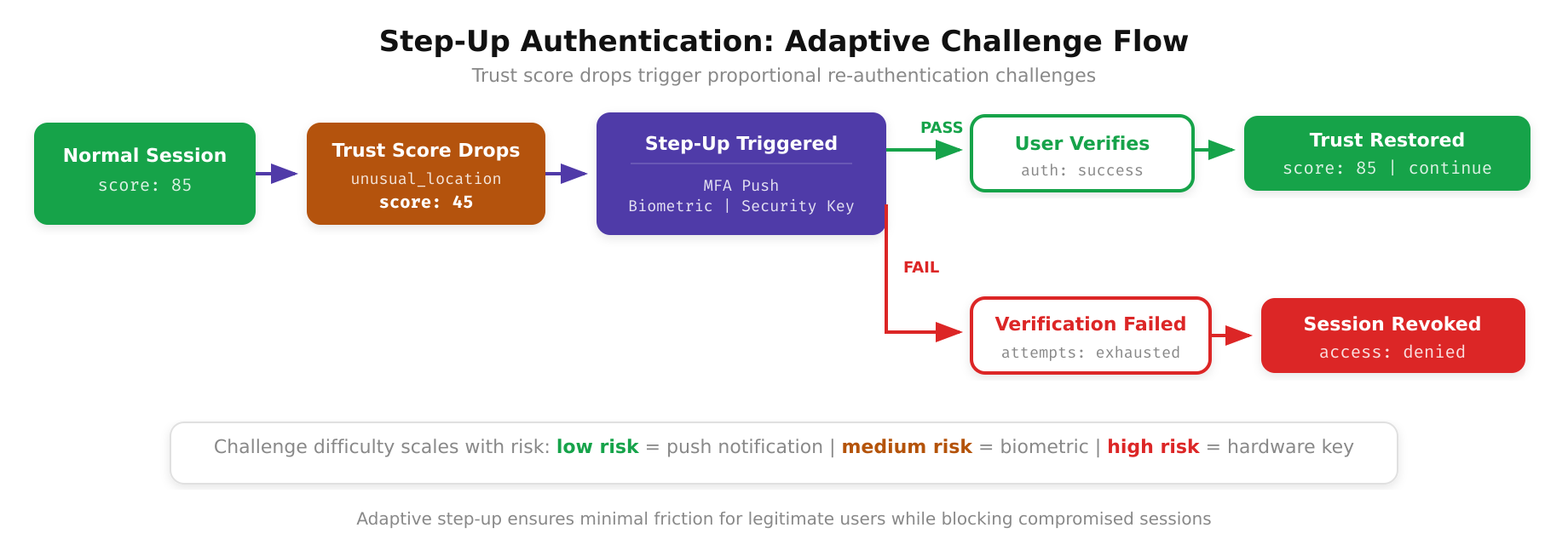
As shown above, the step-up authentication flow operates across graduated risk thresholds. During normal operation, the system passively monitors session signals without user interruption. When the trust score dips below the first threshold, a lightweight challenge such as a FIDO2 prompt is presented. If the score continues to degrade, indicating a more serious anomaly, the system escalates to session scope reduction or full termination with token revocation, ensuring that the response is always proportional to the detected risk level.
Implementation Considerations and Common Pitfalls
Deploying continuous authentication is not without challenges. The most common pitfall is alert fatigue caused by overly aggressive step-up policies. If users are prompted for re-authentication every time their IP address shifts due to carrier-grade NAT or Wi-Fi roaming, they will either abandon the system or find workarounds that weaken security. Tuning the scoring model requires extensive baseline data collection, ideally 30 to 90 days of normal operational telemetry before enforcement policies are activated.
Latency is another critical concern. Every millisecond added to the evaluation pipeline is a millisecond added to request latency. Organizations must benchmark their stream processing infrastructure under peak load and ensure that the 99th percentile evaluation time remains below their acceptable threshold, typically 50 to 100 milliseconds for interactive workloads.
- Start with a shadow mode deployment where the system logs decisions but does not enforce them. Analyze false positive rates before enabling enforcement.
- Define clear signal weighting policies per resource classification tier. Not every resource needs the same level of continuous scrutiny.
- Implement a feedback loop where security analysts can flag false positives and retrain the scoring model.
- Ensure that the step-up authentication mechanism supports multiple modalities (FIDO2, push, TOTP) so that users have fallback options.
Continuous Authentication and Compliance Alignment
From a compliance perspective, continuous authentication directly supports several regulatory requirements. NIST SP 800-207 explicitly calls for continuous verification of trust as a core tenet of Zero Trust architecture. PCI DSS 4.0 requirement 8.3.6 mandates that authentication factors are re-verified when access conditions change. HIPAA’s administrative safeguards under 45 CFR 164.312(d) require mechanisms to verify the identity of persons seeking access to electronic protected health information, which continuous authentication satisfies more robustly than session-based models.
For organizations operating under FedRAMP, continuous authentication provides auditable evidence that access decisions are made dynamically based on current conditions rather than static credentials. This aligns with the Continuous Diagnostics and Mitigation (CDM) program’s emphasis on real-time awareness of the cybersecurity posture of federal systems.
Continuous authentication is not a product you purchase. It is an architectural pattern that integrates identity providers, device management platforms, network telemetry, and policy engines into a cohesive system. The organizations that implement it successfully are those that treat it as a long-term capability investment rather than a point solution deployment.