Why the Traditional Perimeter Is Dead
For decades, enterprise security architecture relied on the castle-and-moat model: a hardened network perimeter with firewalls, DMZs, and VPN concentrators protecting internal assets. The assumption was simple — everything inside the perimeter is trusted, everything outside is not. That assumption collapsed under the weight of cloud migration, remote workforces, SaaS adoption, and the explosive growth of API-driven microservices. When your data lives in AWS S3, your applications run on Kubernetes clusters across three regions, and your employees authenticate from coffee shops in twelve countries, the network boundary ceases to be a meaningful security construct.
The shift to identity as the new perimeter is not a marketing slogan. It is a fundamental re-architecture of how trust is established, verified, and maintained. In a Zero Trust model, every access request is evaluated based on who is requesting, what they are requesting, from where, on what device, and under what conditions. Identity becomes the control plane through which all authorization decisions flow.
Free to use, share it in your presentations, blogs, or learning materials.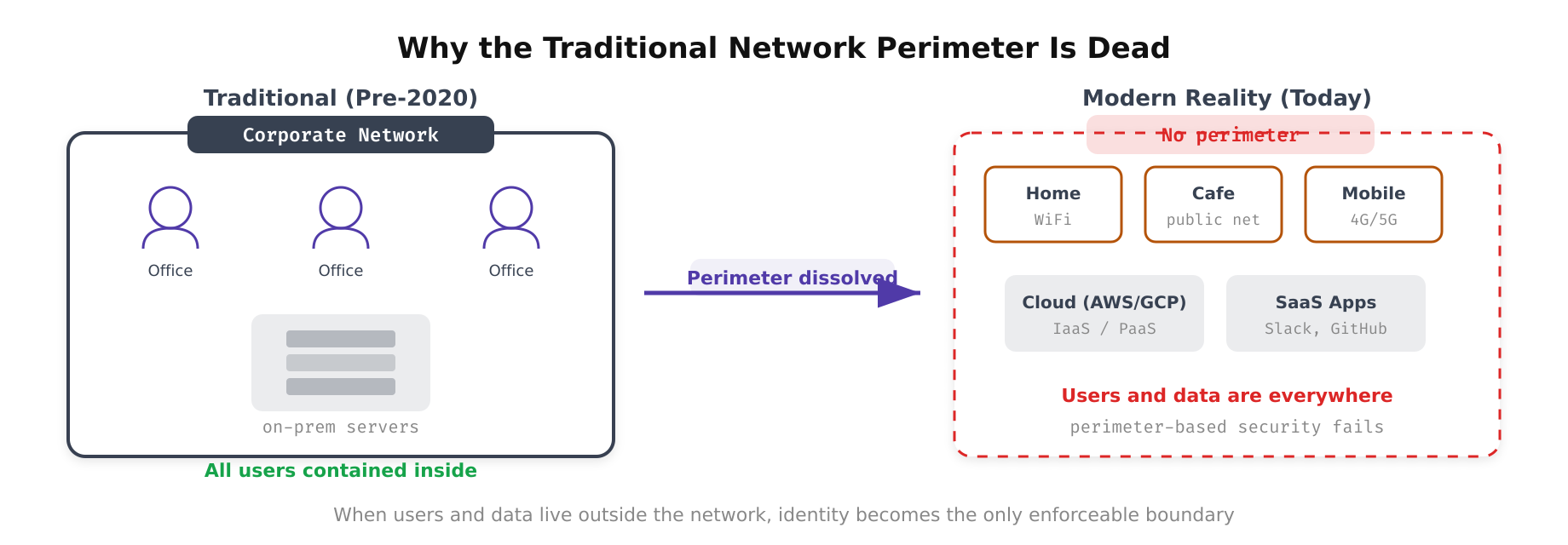
The above illustration depicts how modern workforce patterns have dismantled the traditional network perimeter. Remote workers, cloud-hosted services, SaaS applications, and BYOD devices all bypass the conventional firewall boundary, making network-location-based trust fundamentally unreliable.
Identity as a Control Plane: Core Concepts
When we refer to identity as the new perimeter, we mean that the Identity Provider (IdP) replaces the firewall as the primary enforcement point. Every request — whether it originates from a human user, a service account, a CI/CD pipeline, or an IoT sensor — must present a verifiable identity before accessing any resource. This identity is then evaluated against a set of policies that consider multiple signals.
- Authentication: Proving you are who you claim to be, typically through multi-factor authentication (MFA), certificates, or biometrics.
- Authorization: Determining what resources the authenticated identity can access, governed by RBAC, ABAC, or policy engines like Open Policy Agent (OPA).
- Context evaluation: Assessing device posture, geolocation, time of access, risk score, and behavioral patterns before granting access.
- Continuous verification: Re-evaluating trust throughout a session rather than relying on a single authentication event at session initiation.
This model shifts the enforcement point from a static network boundary to a dynamic, policy-driven decision engine that travels with the identity itself. A user authenticated via a managed device from a corporate network with a clean risk score might receive broad access. The same user on an unmanaged device from an unfamiliar location would receive restricted access or be denied entirely.
Free to use, share it in your presentations, blogs, or learning materials.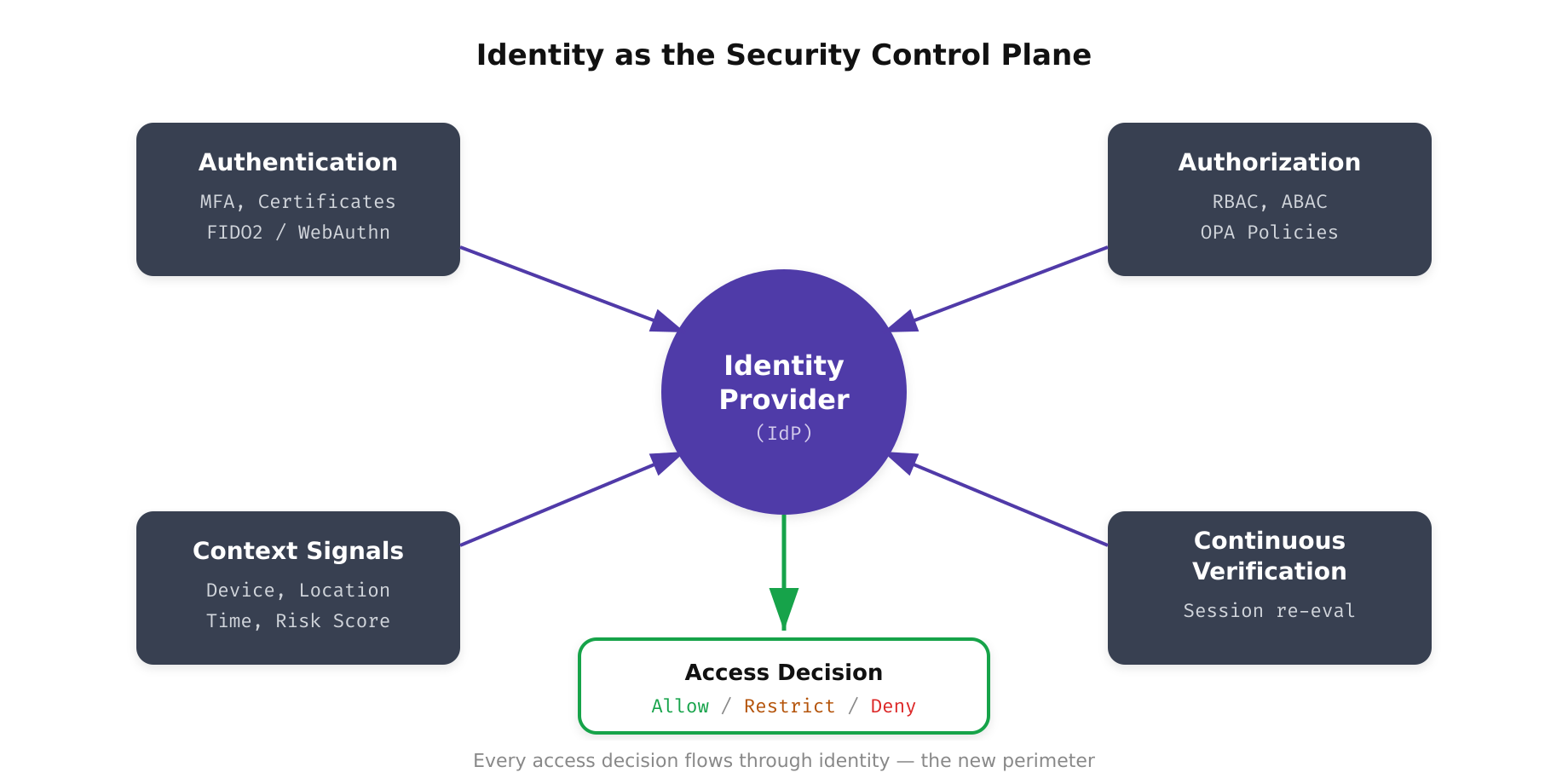
The above illustration shows how the Identity Provider replaces the traditional network perimeter as the central security control plane. Four signal categories, authentication strength, authorization policies, contextual signals, and continuous verification, feed into the IdP to produce a dynamic access decision for every request.
Building the Identity Foundation
Implementing identity as the perimeter requires a robust identity infrastructure. This begins with selecting and deploying an Identity Provider that serves as the authoritative source of truth for all identities in your environment. Modern IdPs such as Azure Active Directory (now Entra ID), Okta, or Keycloak provide centralized authentication, single sign-on (SSO), and policy enforcement capabilities.
Directory Consolidation
Most enterprises suffer from identity sprawl — multiple Active Directory forests, standalone LDAP directories, application-specific user databases, and cloud-native identity stores. The first step is consolidating these into a unified identity fabric. This does not necessarily mean a single directory, but rather a federated model where identities are authoritatively managed in one place and propagated via standards like SCIM (System for Cross-domain Identity Management) to downstream systems.
A practical approach involves deploying an identity governance platform that synchronizes identities from HR systems (Workday, BambooHR) as the authoritative source, provisions accounts into the IdP via SCIM, and automates lifecycle events such as onboarding, role changes, and offboarding. When an employee’s role changes in the HR system, their access should be automatically adjusted across all integrated systems within minutes, not days.
Free to use, share it in your presentations, blogs, or learning materials.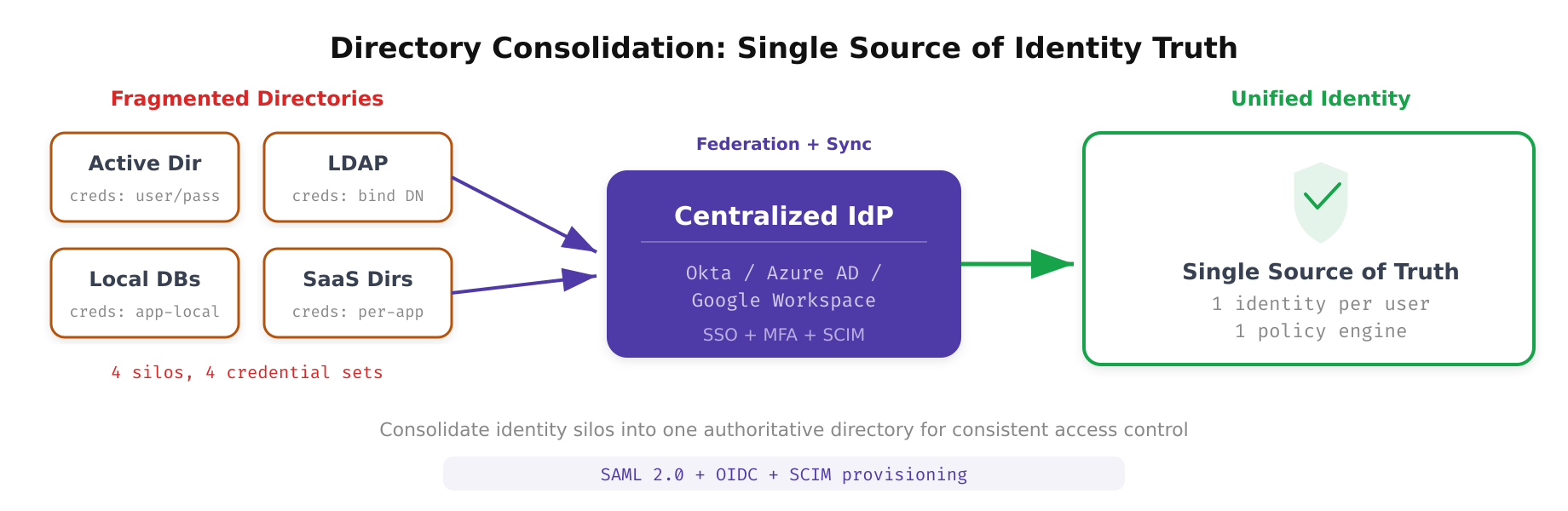
This diagram highlights the process of consolidating disparate identity stores, Active Directory forests, standalone LDAP directories, and application-specific user databases, into a unified Identity Provider. The federated model uses SCIM to propagate identity changes from an authoritative HR source across all downstream systems.
Machine and Workload Identities
Identity-centric security must extend beyond human users to encompass machine identities. In modern infrastructure, non-human identities outnumber human identities by a factor of 10 to 50. These include service accounts, API keys, TLS certificates, Kubernetes service accounts, cloud IAM roles, and CI/CD pipeline credentials. Each of these must be treated as a first-class identity with its own lifecycle management, rotation policies, and access controls.
Tools like HashiCorp Vault, SPIFFE/SPIRE (Secure Production Identity Framework for Everyone), and cloud-native solutions such as AWS IAM Roles for Service Accounts (IRSA) provide mechanisms for issuing, rotating, and revoking machine identities. SPIFFE, in particular, provides a standardized identity framework for workloads that issues short-lived X.509 certificates (SVIDs) to services, enabling mutual TLS authentication without managing long-lived secrets.
Policy Enforcement Architecture
With identity established as the control plane, the next layer is policy enforcement. Every access request passes through a Policy Decision Point (PDP) that evaluates the request against a set of rules. The architecture follows the NIST 800-207 Zero Trust model with three core components.
- Policy Engine (PE): The decision-making component that evaluates access requests against defined policies. This can be implemented using tools like OPA/Rego, Cedar (AWS Verified Permissions), or custom policy engines.
- Policy Administrator (PA): Manages the lifecycle of policies, distributing them to enforcement points and maintaining version control. Infrastructure-as-code tools like Terraform and GitOps workflows ensure policy changes are reviewed, tested, and auditable.
- Policy Enforcement Point (PEP): The inline component that intercepts requests and enforces the PE’s decisions. This can be an API gateway, a service mesh sidecar (Envoy/Istio), a reverse proxy, or an identity-aware proxy like BeyondCorp Enterprise or Pomerium.
A concrete example: when a developer attempts to access a production database, the request hits the PEP (an identity-aware proxy). The PEP extracts the developer’s identity token, queries the PE with the identity, requested resource, device posture data, and current time. The PE evaluates this against policies that might state: “Production database access requires MFA within the last 30 minutes, a managed device with disk encryption enabled, and an active on-call rotation assignment.” The PE returns allow or deny, and the PEP enforces it.
Free to use, share it in your presentations, blogs, or learning materials.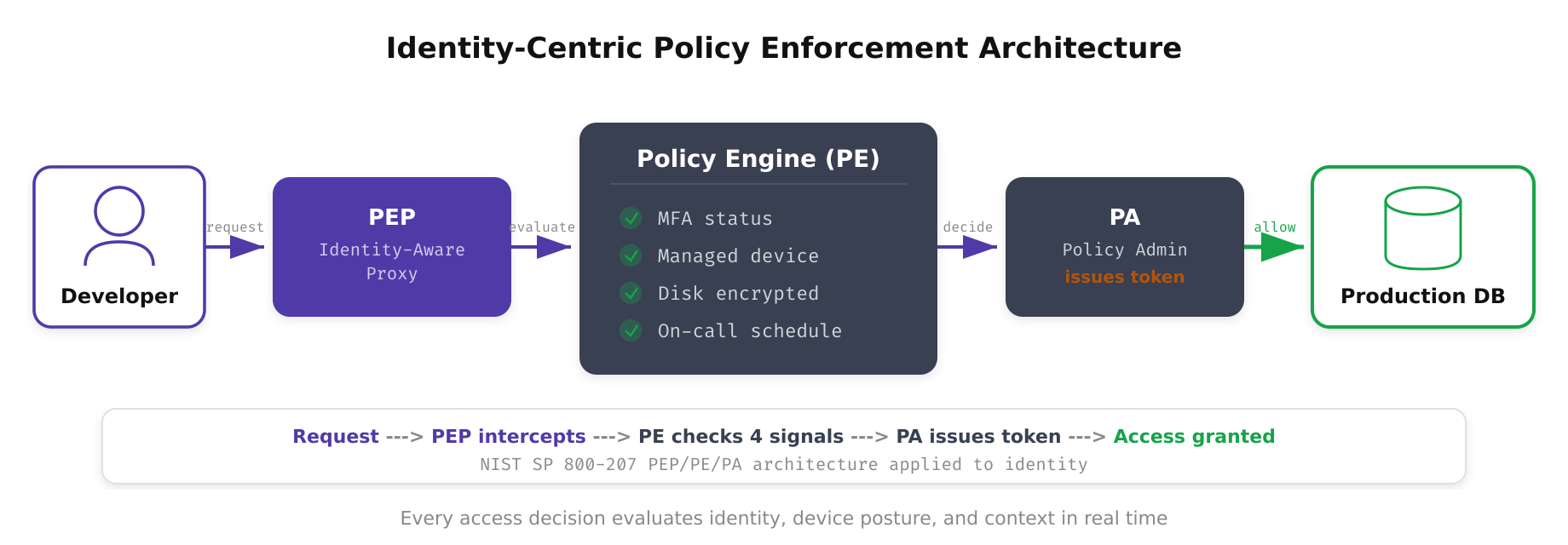
As shown above, the policy enforcement architecture places the Policy Decision Point (PDP) and Policy Enforcement Point (PEP) at the core of every access flow. The PEP intercepts requests inline, while the PDP evaluates identity tokens, device posture, and contextual signals against defined policies to produce allow or deny decisions in real time.
Real-World Implementation Patterns
Google’s BeyondCorp initiative remains the canonical example of identity-as-perimeter at scale. Google eliminated its VPN entirely, routing all employee access through an identity-aware proxy that evaluates device trust, user identity, and context for every request. Employees access internal applications from any network — corporate, home, or public — with identical security controls applied.
For organizations without Google’s engineering resources, a phased approach is practical. Start by deploying an identity-aware proxy in front of your most sensitive internal applications. Migrate VPN-dependent access to the proxy, enforce MFA and device posture checks, and gradually expand coverage. Tools like Cloudflare Access, Zscaler Private Access, and Tailscale provide managed identity-aware access solutions that can be deployed incrementally.
A common pattern for Kubernetes-native environments involves deploying an OIDC-compliant identity provider, configuring the Kubernetes API server to validate OIDC tokens, using admission controllers (Gatekeeper/Kyverno) to enforce identity-based policies on workload deployments, and implementing a service mesh with mTLS for east-west traffic authentication. This ensures that every interaction — human-to-cluster, service-to-service, and pod-to-external-API — is authenticated and authorized through the identity control plane.
Challenges and Operational Considerations
Shifting to identity-centric security introduces operational complexity. Identity infrastructure becomes a critical dependency — an IdP outage can lock out your entire organization. High availability, geographic redundancy, and fallback authentication mechanisms are essential. You need runbooks for IdP failure scenarios and should conduct regular disaster recovery drills.
- Token management: Short-lived tokens reduce the blast radius of credential theft but increase the frequency of authentication events. Implement efficient token caching and renewal mechanisms to avoid performance degradation.
- Legacy system integration: Not all systems support modern identity protocols. For legacy applications that rely on IP-based allowlists or static credentials, deploy identity-aware proxies that translate modern authentication into legacy-compatible formats.
- Observability: Centralize identity event logging (authentication, authorization decisions, token issuance) into your SIEM. Correlate identity events with network telemetry to detect anomalies such as impossible travel, credential sharing, or token replay attacks.
- User experience: Aggressive authentication requirements can create friction. Balance security with usability through risk-based authentication — step up MFA only when risk signals warrant it, and use transparent mechanisms like device trust certificates for low-risk scenarios.
Identity as the new perimeter is not a product you purchase. It is an architectural pattern that requires rethinking how trust is established across your entire technology stack. The network perimeter served its purpose for an era of static, on-premises infrastructure. In a world of cloud-native, distributed, and API-driven systems, identity is the only perimeter that scales.
