Why Zero Trust Demands a Modern SIEM
A Security Information and Event Management (SIEM) platform is the analytical backbone of any Zero Trust deployment. While Zero Trust generates access decisions at the policy enforcement point and trust scores at the policy decision point, it is the SIEM that correlates these events across time, identity, and infrastructure to surface threats that no single component can detect in isolation. Without SIEM integration, Zero Trust telemetry remains a collection of disconnected signals rather than an actionable security intelligence capability.
Traditional SIEMs were designed to ingest firewall logs and antivirus alerts. Zero Trust demands something fundamentally different: a platform capable of processing high-volume, high-velocity, structured event streams from identity providers, device management platforms, policy engines, API gateways, service meshes, and cloud control planes. The SIEM must correlate an authentication event from Okta with a device posture change from Intune, a policy evaluation from the Zero Trust gateway, and an API access log from the application layer, all within seconds.
Mapping Zero Trust Data Sources to SIEM Ingestion
The first step in SIEM integration is mapping every Zero Trust component to a SIEM data source. Each component produces events with different schemas, volumes, and latency characteristics. A well-planned ingestion architecture accounts for these differences and normalizes events into a common schema before they reach the correlation engine.
Identity Provider Events
Identity providers such as Azure AD, Okta, and Ping Identity expose audit logs through APIs that the SIEM can poll or receive via webhook. Key events include user authentication (success and failure), MFA challenge results, conditional access policy evaluations, token issuance, and administrative changes to user accounts or group memberships. Azure AD, for instance, exposes these through the Microsoft Graph Security API, which can be consumed by Sentinel natively or by third-party SIEMs through a log forwarder.
Device Posture and Endpoint Telemetry
Endpoint Detection and Response (EDR) platforms such as CrowdStrike Falcon, Microsoft Defender for Endpoint, and SentinelOne generate telemetry about process execution, network connections, file modifications, and threat detections. Mobile Device Management (MDM) platforms such as Intune, Jamf, and Workspace ONE provide device compliance status, OS version, encryption state, and certificate validity. These feeds must be ingested into the SIEM and correlated with identity events to determine whether a device’s posture changed before, during, or after a suspicious access event.
Network and Application Layer Events
- Zero Trust Network Access (ZTNA) gateway logs: connection establishment, policy evaluation results, session duration, and bytes transferred.
- Service mesh telemetry from Istio or Linkerd: mTLS handshake outcomes, authorization policy decisions, and inter-service traffic flow metadata.
- API gateway logs from Kong, Envoy, or AWS API Gateway: request routing decisions, rate limiting events, and OAuth token validation results.
- Cloud provider control plane logs: AWS CloudTrail, Azure Activity Log, and GCP Audit Logs capturing administrative actions and resource access events.
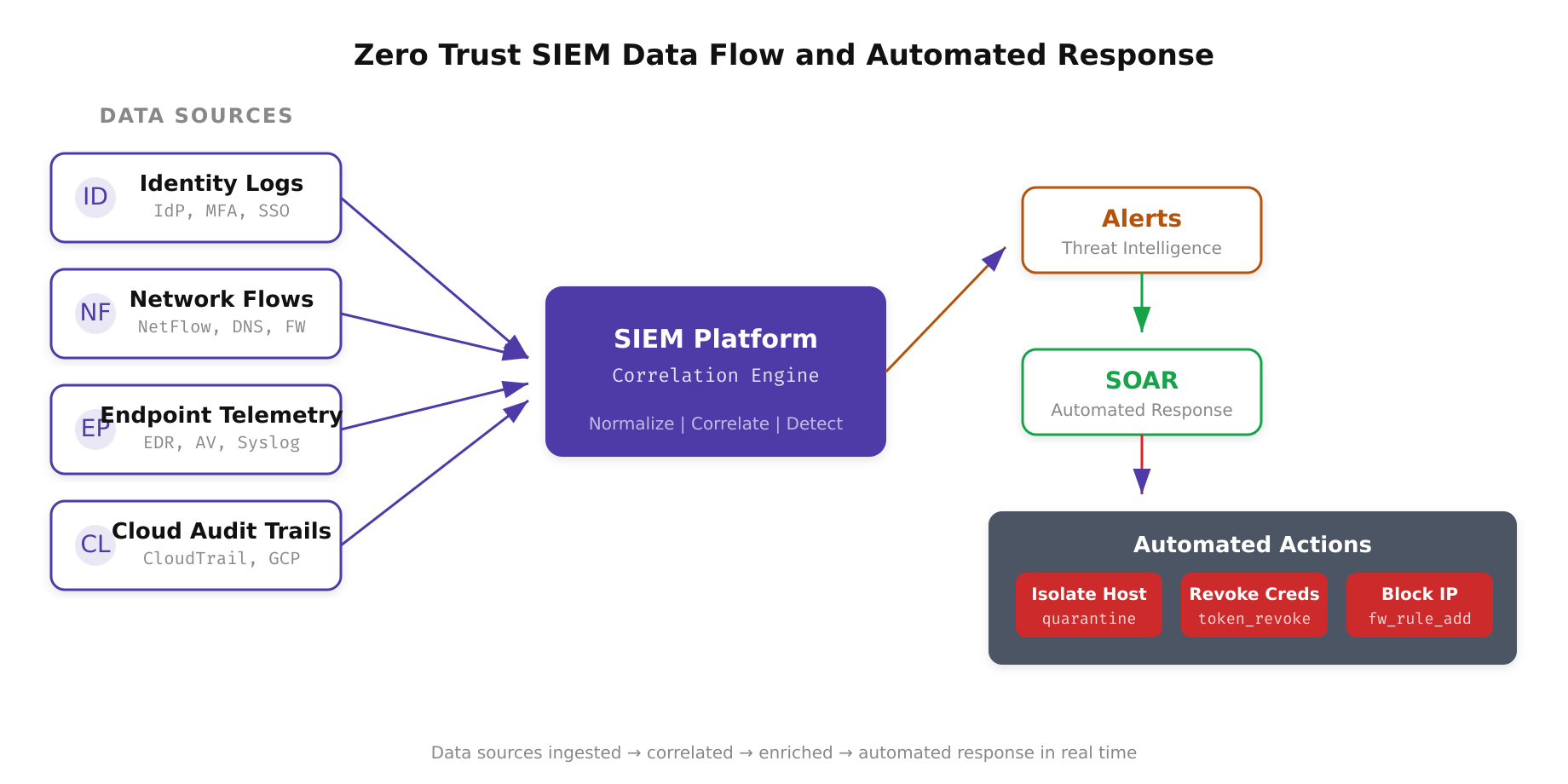
The above illustration shows how a modern SIEM platform sits at the center of Zero Trust observability. Four categories of data sources, identity logs, network flows, endpoint telemetry, and cloud audit trails, converge into the correlation engine. When threat patterns are detected, the SIEM triggers the SOAR platform to execute automated response actions such as host isolation, credential revocation, and firewall rule updates.
Correlation Rules for Zero Trust Detection
The value of SIEM integration is realized through correlation rules that combine events from multiple Zero Trust components into coherent detection logic. These rules encode the relationships between identity, device, network, and application events that indicate compromise or policy violation.
A high-fidelity correlation rule for detecting credential theft might look like this: Alert when a user successfully authenticates from a new device (no prior device registration event) AND the device fails posture compliance checks AND the user accesses a high-sensitivity resource within 10 minutes of authentication AND the user’s historical access pattern does not include this resource. Each condition alone is weak. Together, they produce a high-confidence detection.
Another critical correlation detects policy bypass attempts: Alert when a resource access event is logged at the application layer but no corresponding policy evaluation event exists at the PDP within a 5-second window. This indicates that traffic may have reached the application without passing through the Zero Trust enforcement layer, suggesting a network misconfiguration or an attacker who has found a path around the policy enforcement point.
- Impossible travel: authentication events from geographically distant locations within a timeframe that makes physical travel impossible, correlated with the user’s VPN connection status to exclude legitimate VPN usage.
- Privilege escalation chain: a sequence of role assignment changes, group membership additions, and subsequent access to administrative APIs within a short time window.
- Token replay: the same OAuth access token used from two different source IP addresses within its validity period, indicating potential token theft.
- Device posture degradation during active session: the EDR agent stops reporting or the device falls out of compliance while the user has an active authenticated session to sensitive resources.
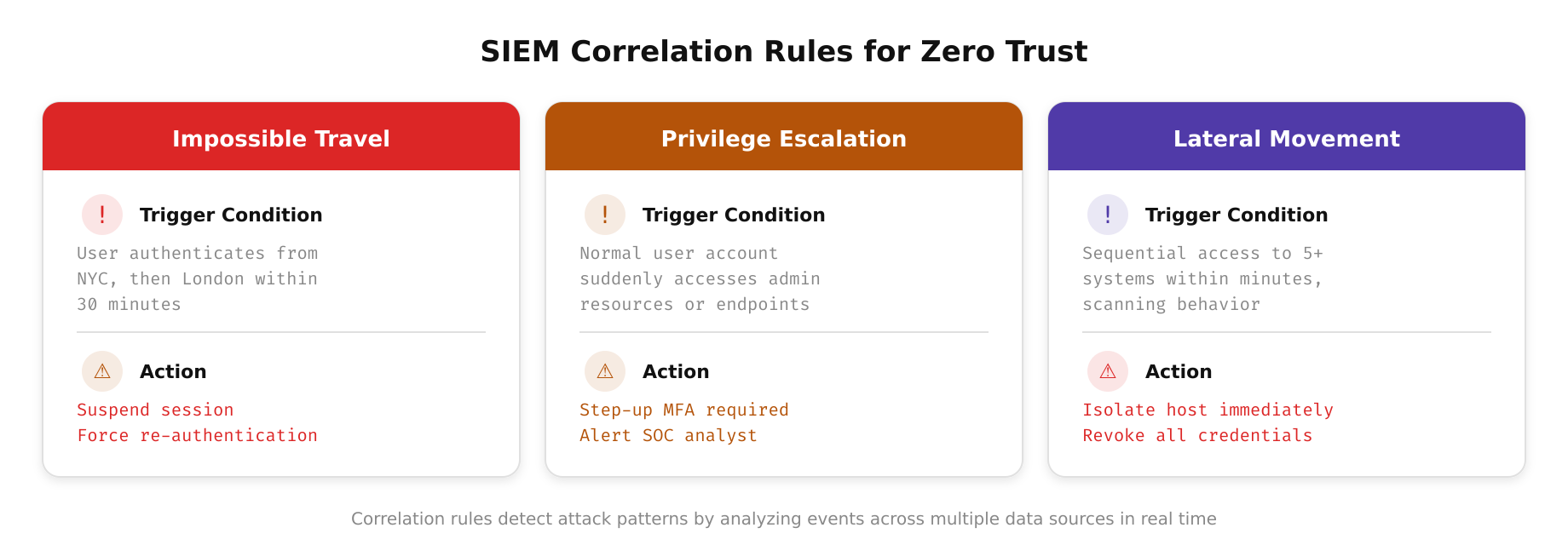
This diagram highlights how SIEM correlation rules combine multiple Zero Trust event streams into high-fidelity detections. Each rule evaluates conditions across identity, device, network, and application layers simultaneously, transforming individual low-confidence signals into actionable alerts that accurately identify credential theft, policy bypass attempts, and lateral movement patterns.
SIEM Architecture Considerations for Zero Trust Scale
Zero Trust generates substantially more telemetry than traditional perimeter security. Every micro-segmented access decision, every policy evaluation, and every trust score computation produces log data. Organizations that deploy Zero Trust across thousands of users and hundreds of microservices can easily generate tens of billions of events per day. The SIEM must be architected to handle this volume without compromising detection latency.
Cloud-native SIEMs such as Microsoft Sentinel, Google Chronicle, and Panther Security are designed for this scale. They separate storage from compute, allowing ingestion capacity and query performance to scale independently. Sentinel’s integration with Azure Data Explorer enables petabyte-scale log retention with sub-second query response times for structured data. Chronicle’s security data lake approach normalizes events at ingestion time using the Unified Data Model (UDM), which reduces query complexity and enables retroactive detection when new threat intelligence becomes available.
For organizations using on-premises or hybrid SIEMs such as Splunk or Elastic Security, capacity planning must account for the 3x to 10x increase in event volume that Zero Trust produces compared to traditional logging. This impacts license costs (for volume-based pricing), storage requirements, and indexing infrastructure. Many organizations adopt a tiered storage strategy where high-priority events (authentication, policy decisions, high-sensitivity access) are indexed in the hot tier for real-time search, while lower-priority events (routine API calls, low-sensitivity access) are stored in a cold tier and queried only during investigations.
Free to use, share it in your presentations, blogs, or learning materials.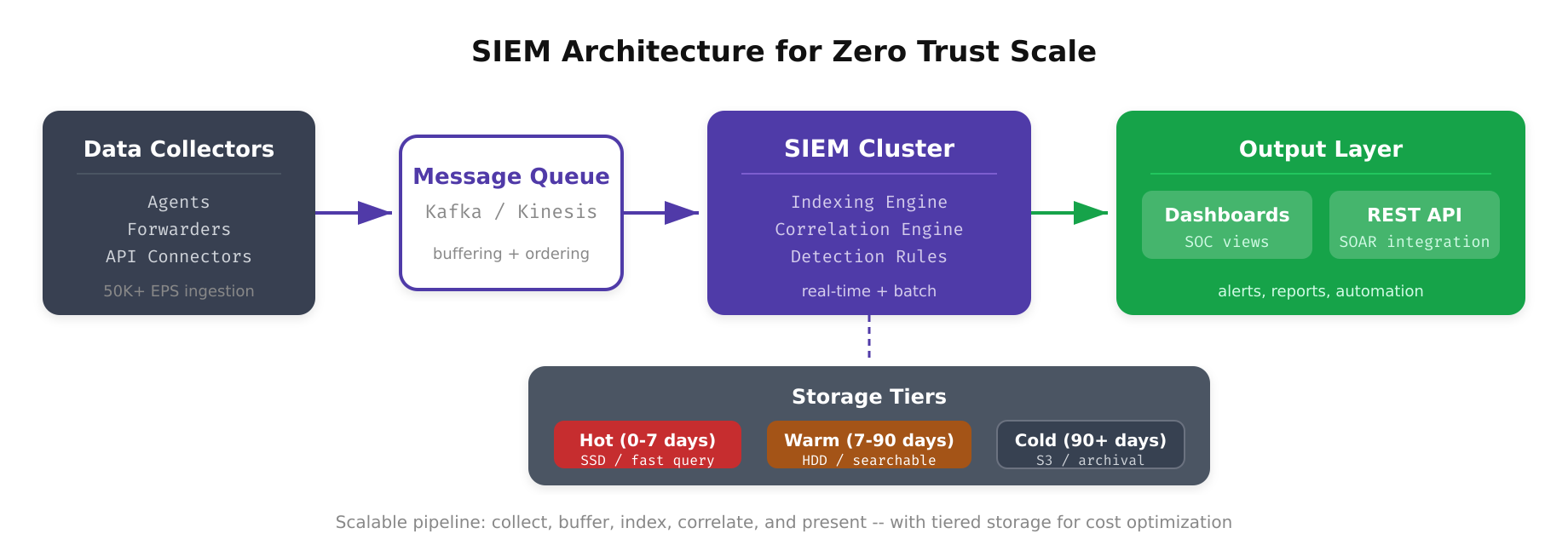
As shown above, a Zero Trust-ready SIEM architecture separates ingestion, normalization, storage, and analysis into distinct layers that scale independently. Log collectors gather events from identity providers, endpoint agents, network gateways, and cloud control planes. Parsers normalize these into a unified data model before routing them to hot or cold storage tiers based on priority, while the correlation engine continuously evaluates incoming events against detection rules.
Automating Response Through SIEM-SOAR Integration
The final stage of SIEM integration in a Zero Trust environment is connecting detection to automated response through Security Orchestration, Automation, and Response (SOAR) platforms. When a SIEM correlation rule fires, the SOAR platform executes a predefined playbook that can revoke tokens through the identity provider API, quarantine a device through the MDM API, add a network block rule through the ZTNA gateway API, create an incident ticket, and notify the on-call security analyst via Slack or PagerDuty.
This automated response loop is what transforms the SIEM from a passive monitoring tool into an active component of the Zero Trust enforcement architecture. The time between detection and containment shrinks from hours (manual triage) to seconds (automated playbook execution). In a Zero Trust environment where the adversary is assumed to already be inside the network, this reduction in mean time to respond is the difference between a contained incident and a full-scale breach.
Free to use, share it in your presentations, blogs, or learning materials.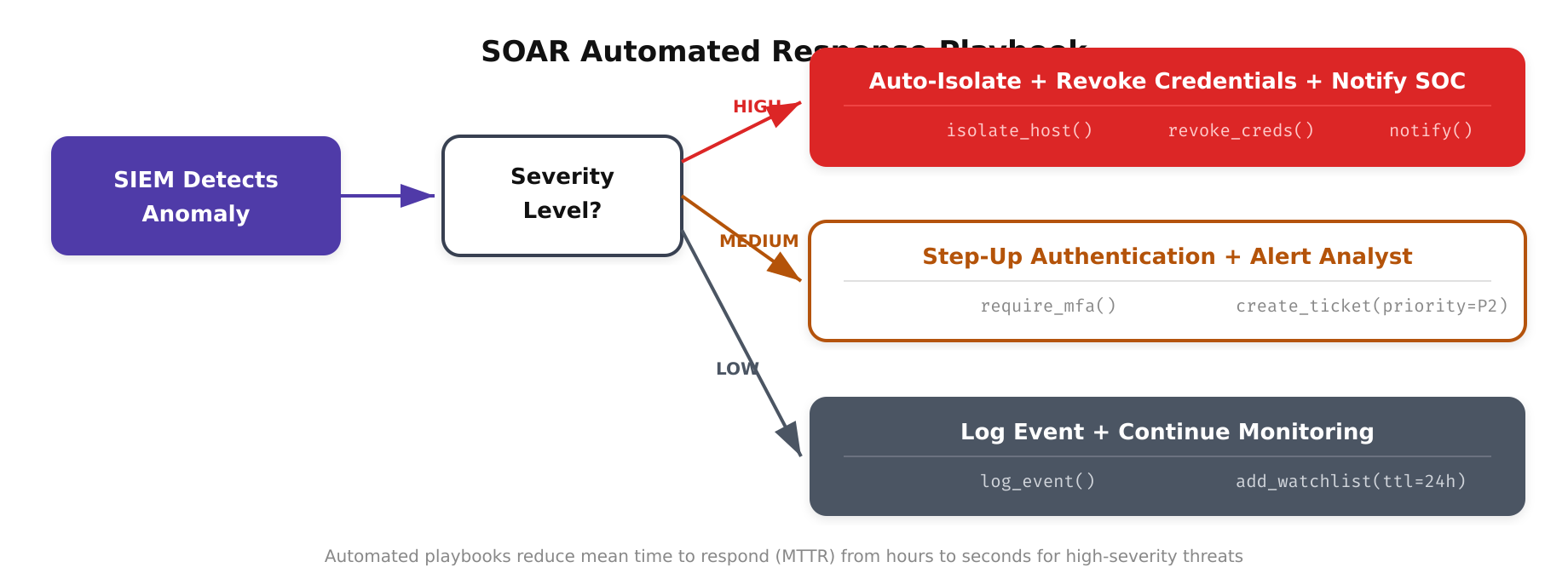
The above illustration depicts the end-to-end SOAR playbook workflow triggered by a SIEM correlation alert. The automated sequence progresses through alert enrichment (pulling context from threat intelligence feeds and asset inventories), investigation (correlating related events across a configurable time window), containment (revoking tokens, isolating hosts, and updating firewall rules via API), and remediation (creating incident tickets and notifying response teams), all executing within seconds of the initial detection.
SIEM integration is not a bolt-on capability for Zero Trust. It is an integral architectural component that provides the correlation, detection, and response capabilities without which Zero Trust policies are enforced but never verified. The investment in SIEM integration pays dividends in detection accuracy, response speed, and the confidence that your Zero Trust architecture is functioning as intended.